The right to an anonymous vote is a cornerstone of the U.S. democratic process. Yet from the time until you walk into the voting booth until long, long after you cast your ballot, your personal information is a highly sought-after commodity. Often your name, contact details, and political leanings are frighteningly easy for political campaigns to access, collect, share, trade, and sell.
First, a caveat. As a 501(c)(3) tax-exempt organization, we are prohibited from electioneering, i.e., endorsing or opposing any particular candidate. So while we’ll offer some illustrative examples, none of what follows is intended to single out any particular candidate—candidates and independent campaign committees across the political spectrum are collecting information about you. This post is not intended to influence your vote, but rather to inform you as a citizen about the privacy implications of your participation in the democratic process. Data collection is an entrenched part of how modern political campaigns work, and that should concern you regardless of your political affiliation.
There’s a theory that the more candidates reach potential voters, the better informed and engaged the voting public might become. That's a double-edge sword: candidates aren’t just gathering information on their potential supporters; they are also investigating their opponents’ supporters.
We should also emphasize that this isn’t just about presidential elections. Even if the presidential field is narrowing, 469 Congressional seats are up for election, plus thousands more on the state and local levels. All of those candidates want your information too.
Public Information
Many people think voter records are completely private. In reality, most states allow campaigns to obtain voter lists, including every registered voter, along with their addresses, party registration and voting history (whether they voted in an election or not, but not how they voted). In Minnesota, you can buy this information from the Secretary of State on CD-ROM for $46, while in Iowa, it can cost nearly $2,000. This is one of the key ways that campaigns are able to gather information on citizens and to determine whether someone is a “likely” voter or not.
Much of this information is classified as public by default, but some information in your voter file—such as your Social Security number—is supposed to be kept private. Unfortunately, data breaches do happen: the Secretary of State of Georgia is facing a lawsuit after his staff accidentally sent CD-ROMS to campaigns containing individuals’ Social Security numbers.
Voter information is not the only information that’s public by default. Campaigns, especially candidate campaign committees, are required to report information on donors to election authorities such as the Federal Elections Commission. Typically this information contains the person’s name, employer, job title, and city where the person lives. Under Federal Elections Commission regulations, federal presidential campaigns must identify donors who contribute more than $200. As an individual, you can only donate up to $100 in cash. You can also donate up to $50 anonymously. Nationally, however, campaign finance disclosure limits vary substantially from state to state, county to county, city to city.
Your level of privacy also depends on the type of process employed in your state. Traditional elections involve private ballots, but caucuses—such as Iowa’s—require a voter to publicly disclose their affiliation by standing in a particular corner of a room at a precinct.
Data Brokers and Campaign Tracking
University of Victoria researcher Colin J. Bennett's excellent paper, “Trends in Voter Surveillance in Western Societies: Privacy Intrusions and Democratic Implications,” outlines how emerging technology are allowing campaigns to collect more and more information on voters:
[T]he analysis and profiling of voters is increasingly supplemented by data on consumers, and the mining of those data to target increasingly narrower slices of the electorate in key electoral districts. Politicians shop for votes, and increasingly find data on consumers increasingly valuable in that endeavor. Where voter surveillance begins and consumer surveillance ends is increasingly difficult to determine.
Although consumers have become more aware of data brokers collecting browsing and shopping patterns online over the last few years, political campaigns have been compiling, sharing, buying, and selling voter lists for decades. For example, a company called Response Unlimited has been compiling lists of conservative voters for more than 35 years, selling them to campaigns and advocacy groups for the purposes of direct mail solicitation. These lists often reveal highly personal information about people, including their religion, political priorities, and donation habits. For example, a campaign might buy access to lists such “Catholic households,” “veteran donors,” and “Second Amendment active supporters.”
In addition to third-party brokers, campaigns themselves trade the contact details they collect. That’s why you often hear in political press how valuable Obama’s voter database is to candidates. Just before Christmas, the Democratic primary race was thrown into tumult after allegations that Sen. Bernie Sanders’ campaign had accessed voter data in a Democratic National Committee database that was supposed to be firewalled for his opponent Secretary Hillary Clinton’s campaign.
On the Republican side, security researcher Robert Graham identified how email addresses were being shared among candidates. As Graham wrote on his blog, he creates a new email address for every candidate’s newsletter. Shortly after Texas Gov. Rick Perry dropped his 2016 bid for president, Graham started getting emails to that account from Sen. Ted Cruz’s campaign, indicating that the Perry campaign’s email database had been shared, lent, or sold.
Cruz’s campaign has been both praised and criticized for its data collection and analysis through a firm called Cambridge Analytica. As Associated Press reported after analyzing several candidates’ data gathering efforts:
The scope of Cruz's system is formidable. Cambridge's database combines government and commercial data sets such as voter rolls and lists of people who liked certain Facebook posts, along with consumer data from grocery chains and other clients that can provide a voter's preferred brand of toothpaste or whether he clips coupons. In Iowa, where identifying evangelical voters was key to Cruz's victory strategy, Cambridge's employees scoured the Internet for such useful information as church membership rolls.
Cambridge CEO Alexander Nix said the company categorizes every American into one of five basic personality types derived from academic research and up to 50,000 questionnaires conducted each month.
"We've quantified the personalities of every adult American," Nix said. "We can reach out and target those different clusters with messages about the things they care about most, but that have been nuanced to resonate with their personality type."
Campaigns have also deployed apps to help their supporters gather data. Cruz’s campaign uses a mobile app called “Cruz Crew,” which AP reported had been downloaded more than 61,000 times as of February 11. Candidates Ben Carson, Gov. John Kasich, and Sen. Bernie Sanders use apps that collect similar types of data and track the movements (i.e. location) of supporters.
Online Tracking
A leak from former Florida Gov. Jeb Bush’s campaign provided a window into the ways campaigns are tracking individual voters.
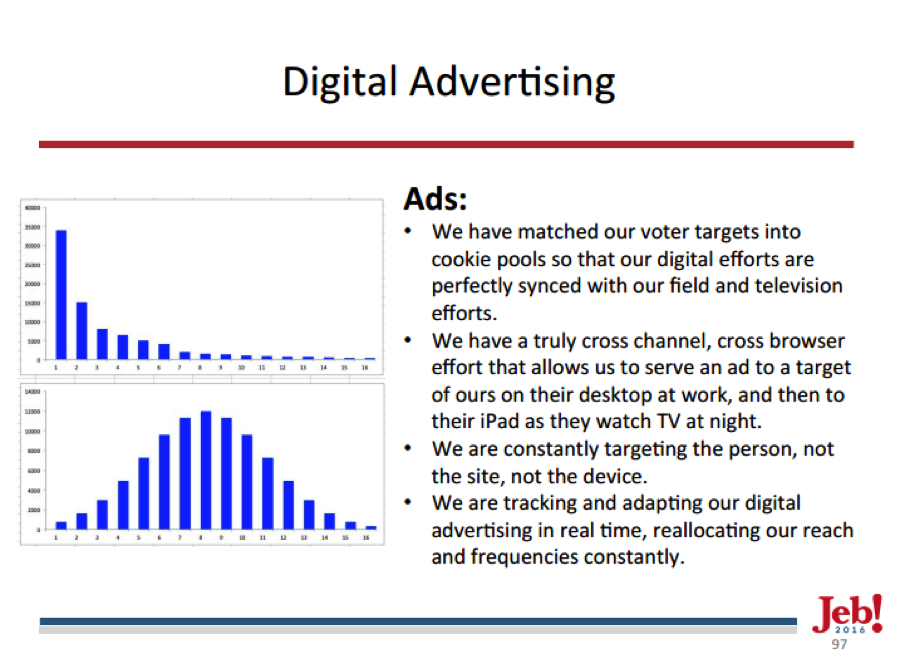
According to the slide deck, Bush’s campaign was “constantly targeting the person, not the site, not the device,” with a system that allows the campaign “to serve an ad to a target of ours on their desktop at work, and then to their iPad as they watch TV at night.” This practice was likely not unique to Bush’s campaign: if you’ve clicked on a candidate’s website and almost instantly noticed an uptick in that candidate’s ads on Facebook, chances are you are being tracked.
In September, the Online Trust Alliance released a “Presidential Candidate Online Trust Audit” showing that 74% of the field of presidential candidates’ websites engage in poor privacy practices:
Some websites failed due to nonexistent or inadequate privacy policy disclosures. Others flunked because they reserve the right to liberally share or sell their donors and site visitors’ personally identifiable information (PII), including addresses, phone numbers, employers and even passport numbers, with unaffiliated third parties that the candidates deem as like-minded organizations.
A quick check of the remaining presidential candidates’ websites using Privacy Badger shows that each runs average of six potential tracking cookies. All of the candidates acknowledge as much on their sites, with Donald Trump, Sen. Bernie Sanders, and Sec. Hillary Clinton going one further in their privacy policies to disclose the use of web beacons, such as pixel tags or clear gifs, to track users across websites.
The Fine Print
It’s never a bad idea to read any commercial website’s privacy policies and terms of use. You might even find some positive disclosures. For example, Gov. Rick Santorum’s site allows users to email his campaign to review what information it has collected on you and make corrections. Jeb Bush’s site similarly offered the ability to see what information was collected, plus an an opt-out feature (although the link was broken for much of his campaign).
But if you do read the fine print, you might find that these agreements can affect not only your personal privacy, but how your ideas might be used. For example, both Sen. Rand Paul and former Secretary of State Hillary Clinton’s website terms of use employ the same boiler plate language when it comes to the communications you send to the campaigns.
From the defunct Rand Paul for President website:
You acknowledge and agree that any feedback, questions, comments, suggestions, ideas, or other information or materials regarding the Sites or Rand Paul for President that are provided by you in the form of email or other submissions to Rand Paul for President, or any postings on the Sites, are non-confidential and shall become the sole property of Rand Paul for President. Rand Paul for President shall own exclusive rights, including all intellectual property rights, and shall be entitled to the unrestricted use and dissemination of these materials for any purpose without acknowledgment or compensation to you.
From Hillary for America (HFA):
You acknowledge and agree that any feedback, questions, comments, suggestions, ideas, or other information or materials regarding the Site or HFA that are provided by you in the form of email or other submissions to HFA, or any postings on the Sites, are non-confidential and shall become the sole property of HFA. HFA shall own exclusive rights, including all intellectual property rights, and shall be entitled to the unrestricted use and dissemination of these materials for any purpose without acknowledgment or compensation to you.
In other words, if you write a poem about drone strikes or a song about raising the minimum wage and send it to one of these campaigns, it is the campaign's position that your creation belongs exclusively to them. We found similar language on a variety of campaign sites, including two political party sites in India.
Emerging Technology
New and chilling technological practices have emerged in just the past few months. One of the most frightening so far was a claim by a firm called Dstllery that it had captured the mobile device IDs from Iowa caucus goers and then matched them to their online profiles. They then used this information in combination with precinct results to make assumptions about their voting prefences. As Fusion’s Kashmir Hill reported:
What really happened is that Dstillery gets information from people’s phones via ad networks. When you open an app or look at a browser page, there’s a very fast auction that happens where different advertisers bid to get to show you an ad. Their bid is based on how valuable they think you are, and to decide that, your phone sends them information about you, including, in many cases, an identifying code (that they’ve built a profile around) and your location information, down to your latitude and longitude.
…
So on the night of the Iowa caucus, Dstillery flagged all the auctions that took place on phones in latitudes and longitudes near caucus locations. It wound up spotting 16,000 devices on caucus night, as those people had granted location privileges to the apps or devices that served them ads. It captured those mobile ID’s and then looked up the characteristics associated with those IDs in order to make observations about the kind of people that went to Republican caucus locations (young parents) versus Democrat caucus locations. It drilled down farther (e.g., ‘people who like NASCAR voted for Trump and Clinton’) by looking at which candidate won at a particular caucus location.
As the election progresses, we expect to see techniques like these and ones no one has yet imagined to surface.
What You Can Do
Regardless of your party affiliation or candidate preference, you should be mindful that the information you leave in your wake may be used over and over again in future election cycles. The good news is we have some basic tips for protecting your privacy as you participate in the election or browse candidate websites to seek more information.
- Consider creating a special email account specifically for subscribing to candidate email lists.
- Use Privacy Badger or similar anti-tracking extensions when browsing sites online. You can also use Tor to enhance your privacy.
- Be mindful that under Federal Elections Commission regulations, federal campaigns must identify donors who contribute more than $200. You can donate up to $100 in cash, and up to $50 anonymously.
- Think very carefully before using your social media login to register for campaign sites or apps. Even if you’re happy to share your details with a candidate, your friends and family may not as pleased to learn that you also shared your friends list.
- Be careful when you “like” or “follow” a particular candidate on social media.
- Register to vote directly with your county or state agencies, rather than paid signature gatherers of campaigns.
- Turn off your phone, or at least location services, as you approach voting precincts.
- Be wary of telephone pollsters, particularly if the firm is not well recognized. Gallup, for example, has a public privacy policy, while lesser known polls may be design more to manipulate (“push-polls”) or gather information rather than produce actual analytical data.
- Rather than sharing links from a candidates campaign, paste the link to the Internet Archive's Wayback Machine, then share that link. That way, you're sharing the information without the campaign's trackers attached.
- Think twice before opening the door for a political canvasser bearing a tablet: not only might they be tailoring their message to match your online profile; your interaction will likely be documented for future reference.
- Be mindful of getting all of your political information from a single social media site. As we learned in 2012, Facebook invisibly tweaked its algorithms to see if it could influence voter turnout.
Democracy works only if we participate, and there are lots of ways to do that without sacrificing your privacy. Besides, the more mysterious you are to the candidates, the harder they will have to work to give you more information about themselves, rather than gather information from you.













