 Recently released daily flight logs from Customs & Border Protection (CBP) show the agency has sharply increased the number of missions its 10 Predator drones have flown on behalf of state, local and non-CBP federal agencies. Yet, despite this increase—eight-fold between 2010 and 2012—CBP has failed to explain how it’s protecting our privacy from unwarranted drone surveillance.
Recently released daily flight logs from Customs & Border Protection (CBP) show the agency has sharply increased the number of missions its 10 Predator drones have flown on behalf of state, local and non-CBP federal agencies. Yet, despite this increase—eight-fold between 2010 and 2012—CBP has failed to explain how it’s protecting our privacy from unwarranted drone surveillance.
EFF received the three years of flight logs, a 2010 “Concept of Operations” report about the Predator program (newly-released pages here), and other records in response to our Freedom of Information Act lawsuit against the agency. In that lawsuit we asked for specific information on the agency’s program to loan out its drones to local, state and federal agencies.
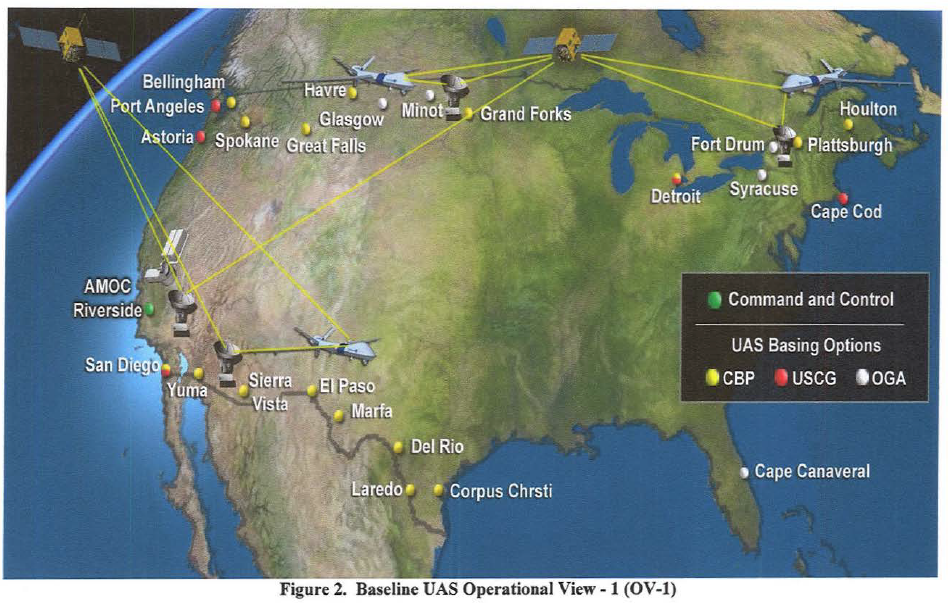
According to the documents, CBP already appears to be flying drones well within the Southern and Northern US borders, and for a wide variety of non-border patrol reasons. What’s more — the agency is planning to increase its Predator drone fleet to 24 and its drone surveillance to 24 hours per day / 7 days per week by 2016.
As the Concept of Operations report notes, CBP’s goal is that its drone data will be “persistently available” (p. 21) and interoperable (p. 29) — not just within CBP, but to other agencies, and also possibly to other countries. CBP plans that its “UAS will provide assured monitoring of entities along land borders, inland seas, littorals and high seas with sufficient frequency, continuity, accuracy, spectral diversity, and data content to produce actionable information.” (p. 29)
Daily Predator Flight Logs Detail Scope of CBP Drone Flights for Other Agencies
CBP’s three years of daily flight logs detail when, where and how the agency flew its Predator drones on behalf of other agencies. These logs show a marked increase in drone flights over the years. In 2010, CBP appears to have flown its Predators about 30 times on behalf of other agencies, but this number increased to more than 160 times in 2011 and more than 250 times in 2012.
While CBP blacked out important information about dates, geographic location of flights, and, in most cases, agency names, these logs do provide some insights into the agency’s drone program. For example, we’ve learned that CBP conducted drone surveillance for law enforcement agencies ranging from the FBI, ICE, the US Marshals, and the Coast Guard to the Minnesota Bureau of Criminal Investigation, the North Dakota Bureau of Criminal Investigation, the North Dakota Army National Guard, and the Texas Department of Public Safety. These missions ranged from specific drug-related investigations, searches for missing persons, border crossings and fishing violations to general “surveillance imagery” and “aerial reconnaissance” of a given location.
CBP also flew its drones for non-law enforcement agencies and missions. The logs show that CBP conducted extensive “electro-optical, thermal infrared imagery and Synthetic Aperture Radar” surveillance of levees along the Mississippi River and river valleys across several states, along with surveillance of the massive Deep Water Horizon oil spill and other natural resources for the US Geological Survey, FEMA, the Bureau of Land Management, the US Forest Service, the Department of Natural Resources, and the National Oceanic and Atmospheric Administration.
Yet even these missions raise red flags. While the goal of each may be to gather useful environmental information, the drones necessarily also collect information on the people living within those areas—and we’ve seen no policies describing limitations on how the information is used or whether it’s shared with law enforcement agencies like the FBI or ICE.
Report Details CBP’s Plans to Increase Surveillance Capabilities, Expand Operations, and Possibly Add Weapons to Drones
CBP also released to EFF a 2010 “Concept of Operations” report for its drone program (newly-released pages here). This document provides significant detail about CBP’s program, including the three major operational locations in which the agency flies its drones, the Predators’ on-board surveillance technologies, and CBP’s "far-term" goals for the program.
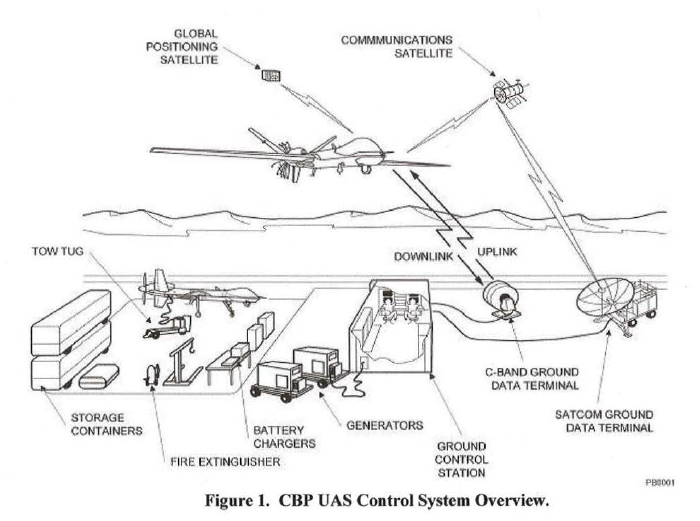 The report notes that CBP’s Predators have highly sophisticated, high resolution Synthetic Aperture Radar (SAR), color video, and electron optical (EO) and infrared (IR) cameras, and are capable of performing Reconnaissance, Surveillance, Targeting and Acquisition (“RSTA”) on and tracking of multiple moving and stationary targets of interest in both clear and adverse weather. CBP hopes to improve its surveillance capabilities in the future so that its sensor “point target resolution” increases to “well below one foot.”
The report notes that CBP’s Predators have highly sophisticated, high resolution Synthetic Aperture Radar (SAR), color video, and electron optical (EO) and infrared (IR) cameras, and are capable of performing Reconnaissance, Surveillance, Targeting and Acquisition (“RSTA”) on and tracking of multiple moving and stationary targets of interest in both clear and adverse weather. CBP hopes to improve its surveillance capabilities in the future so that its sensor “point target resolution” increases to “well below one foot.”
The report also notes that CBP plans to make its drones and the data gathered through its drone surveillance even more widely available to outside agencies. For example, CBP plans to share data on a near real-time basis, possibly “via DOD’s Global Information Grid (GIG)/Defense Information Systems Network.” CBP also plans that “joint DHS and OGA [other government agency] combined operations will become the norm at successively lower organizational hierarchical levels[,]” which will, presumably, reduce the already limited oversight for CBP’s drone-loan program.
As we noted earlier in a separate blog post, one of the most surprising pieces of information revealed in this report is that CBP has considered equipping its predators with “non-lethal weapons designed to immobilize” targets of interest. Predators are designed to carry weapons for use in wars abroad, but this is the first we’ve heard of a federal agency proposing using weapons domestically.
CBP’s Formal Process for Prioritizing Missions is Detailed in a Power Point Presentation
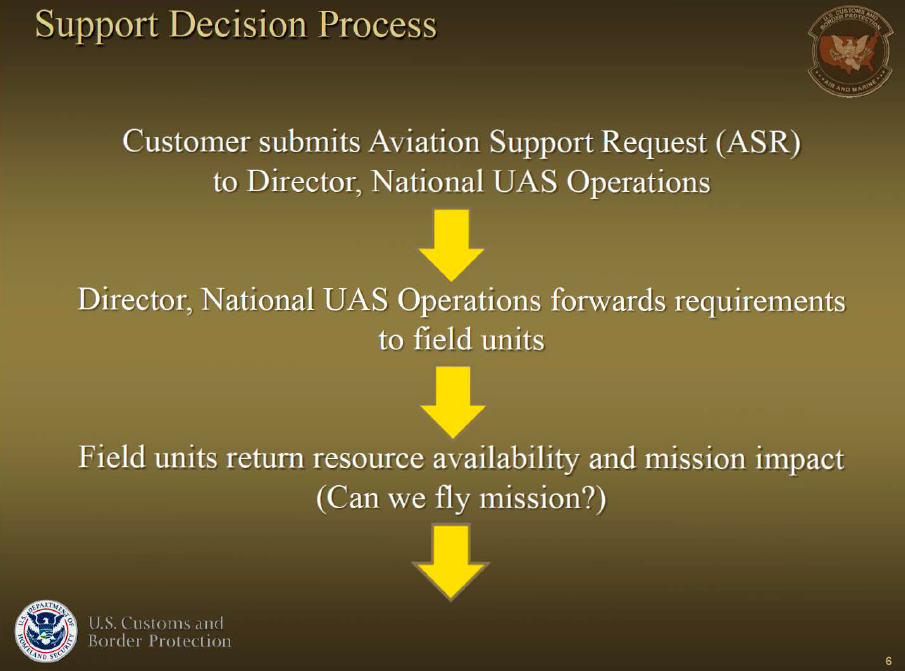 The final document we received from the agency is an October 2012 Power Point document titled “CBP UAS Mission Prioritization Process.” This document describes for the first time CBP’s policies on loaning out its predator drones to other agencies.
The final document we received from the agency is an October 2012 Power Point document titled “CBP UAS Mission Prioritization Process.” This document describes for the first time CBP’s policies on loaning out its predator drones to other agencies.
The document was likely drafted in response to last year’s scathing report (pdf) from the Department of Homeland Security Office of Inspector General. The OIG Report noted several serious problems with CBP’s drone program, including lack of appropriate equipment and staff to fly the drones safely, failure to account and recoup costs for expenditures, and lack of procedures to prioritize requests for drone flights. We noted when the report came out that the agency’s lack of procedures was especially troubling, given the agency has been flying drones since 2004, and that its 10 Predator drones each cost $18 million to purchase and $3,000 per hour to fly.
Considering the scope of the OIG’s criticism of CBP’s drone program, it’s surprising this is the only document the agency has drafted to explain its prioritization process (and CBP has assured us this was the only document, as of last October). The presentation fails to provide much-needed details about the process, including which types of state and local missions CBP feels are appropriate for its drone surveillance (and how the agency determines this), how CBP recoups costs for its involvement in these missions, and how it determines appropriate legal and technical protections are in place to protect privacy and civil liberties.
Conclusion
While these documents provide Americans with important information about CBP’s drone program and the agency’s plans for expanding that program, they raise more questions than they answer. CBP needs to tell Americans where—specifically—it’s flying its drones, which agencies it’s flying its drones for, what it does with the data it collects, and what policies it has in place (if any) to protect our privacy rights. Also, as we’ve detailed in a separate blog post, CBP needs to assure the public that it will not equip its Predators with any weapons—lethal or otherwise. Without first addressing these issues, the agency—and Congress—should halt the expansion of CBP’s Predator drone program.
Documents:
- 2010 “Concept of Operations” Report
- New Pages from 2010 "Concept of Operations" Report
- 2012 CBP UAS Mission Prioritization Process Presentation
- 2011 Daily Flight Logs - Part 1
- 2011 Daily Flight Logs - Part 2
- 2012 Daily Flight Logs - Part 1