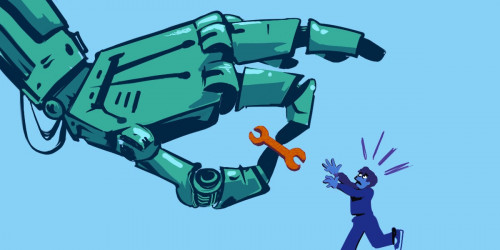
There’s a lot of legitimate concern these days about Internet giants and the lack of competition in the technology sector. It’s still easy and cheap to put up a website, build an app, or organize a group of people online, but a few large corporations have outsized power over the key resources needed to do those things. That, in turn, gives those companies extraordinary power over speech, privacy, and innovation. Indeed, just this week we're learning that Facebook made exclusive data-sharing deals with a few companies, undermining both user privacy and competition in one fell swoop.
Naturally enough, many have looked to antitrust law to provide the right tools to address this problem—and called for legal reform when they discovered that current antitrust approach may not offer those tools. That’s useful and important work.
But antitrust isn’t the only area of law that has a role to play here. And it may not be the easiest one to reform. There at least three other legal doctrines that have an powerful but sometimes hidden effect on tech competition: the Computer Fraud and Abuse Act (CFAA), section 1201 of the Digital Millennium Copyright Act (DMCA), and the unthinking enforcement of so-called “End User License Agreements” that dictate how purchasers can use software.
Any effort to spur competition needs to include reform of these legal tools. And reform of these tools may help in the short run as we consider longer term strategies like updating the rest of competition law. Let’s break it down.
The CFAA and Copycat State Computer Crime Laws
The CFAA was enacted in 1986, when there were only about 2,000 computers connected to the Internet. Motivated in part by Congressional concerns after seeing the movie “War Games,” the law makes it a crime to access a computer connected to the Internet “without authorization.” But because it is so badly written, it has since metastasized in some jurisdictions into an all-purpose tool to criminalize all kinds of normal activities—including failing to abide by computer use policies like click-thru terms of service.
How does CFAA harm competition? Imagine a tool that lets you view, manage, and use all of your social networks in one screen, avoiding the need to shift from one to the other or the need to check whether you’re connected via Facebook, Twitter, or Google+ when you send a friend a message. With your approval, the tool logs you in to your various social networks, seamlessly connects them, and keeps the ads intact. Great innovation, huh? It would be, if it existed.
All too briefly, this tool did exist, thanks to a little company called Power Ventures—until Facebook ran to court to shut it down. In Facebook v. Power Ventures, Facebook noted that it had tried to stop the tool by sending a cease and desist letter and blocking the tool’s IP address. The toolmaker, trying to continue to provide his service, jumped to a new IP address to avoid the block. The social network argued, successfully, that ignoring the cease and desist letter and moving to a new IP address violated the CFAA, resulting in a giant, bankrupting judgment against the company and its founder personally. What is worse, after the decision was issued, companies—almost immediately—started citing the case in cease and desist letters, demanding that competitors stop using automated methods to access even publicly available information on their websites.
Facebook recently changed its policy to allow developers to build competing features upon its own platform, and that’s great. But that shift came too late for Power Ventures. And it’s brittle: Facebook could change it back at any time. Worse, the bad caselaw Facebook created is still out there and being used by other companies. Multiple cases are still pending across the country based on that precedent and other overbroad applications of the CFAA, and the threat letters continue.
CFAA reform is long overdue. Rep. Zoe Lofgren, along with Senator Ron Wyden, has a draft proposal to get some of that done. But we need more. To fix the CFAA, we need to clarify the meaning of "unauthorized" to reflect that commonplace and privacy-protective "circumvention" techniques should not be crimes, and we also need to make penalties proportionate to offenses.
Section 1201
Section 1201 of the Digital Millennium Copyright Act makes it illegal to circumvent any “technological protection measure” (often called TPM or DRM, short for “Digital Rights Management”) that controls access to copyrighted works. It also bans the manufacture and sale of tools to circumvent those digital locks. Although it was pitched as a new legal protection for copyright holders to prevent infringement, the law has given major entertainment companies and other copyright owners lots of control over non-infringing uses of technology, allowing them to lock out competition in repair and re-sale businesses, and to threaten and silence security researchers. The law has some exceptions, but they are far too narrow, vague and complicated for use by anyone who really needs the protection.
The anti-competitive effect of Section 1201 became evident early on with respect to DVDs. The encryption on DVDs was broken almost immediately, as were updated versions. Yet movie studios continued to embrace encryption, using it on every commercial DVD release. Why? Because the movie studios could force innovators to sign a license agreement for that encryption software before they built anything that can decrypt a DVD movie. This gave the movie studios unprecedented power to influence the pace and nature of innovation in DVD technology, and they used it to kill several products, from a “jukebox” like DVD player to an automatic backup software especially loved by people with small kids. The result was that DVD innovation essentially halted in 1998, and stayed in one place long before streaming took over.
But the problem does not stop with DVD technologies. Most modern durable goods—including household appliances, power tools, calculators, cameras, stereos, printer cartridges, garage door openers, as well as video game controllers, headsets, and memory cards—contain some element of copyrightable software code. In order for replacement parts and compatible accessories to function, they often must “access” the code inside, and would-be competitors must “access” that code to reverse engineer it and develop those products in the first place. If unauthorized access amounts to circumvention of a TPM and is therefore prohibited, the manufacturer can use the DMCA to assert exclusive control over the market for those goods and accessories far beyond what any copyright or trade secret law had ever allowed before.
Manufacturers take full advantage. For example:
- Camera makers have installed technological protection measures that render pictures unreadable in competitors’ photo-editing programs, preventing consumers from editing their own pictures with their preferred software – and thereby ensuring that software never enters the market.
- Lexmark, the second-largest laser printer maker in the U.S., added authentication routines between its printers and cartridges explicitly to hinder aftermarket toner vendors. When a competitor, Static Control Components (SCC), reverse-engineered these measures and sold “Smartek” chips that enabled refilled cartridges to work in Lexmark printers, Lexmark used the DMCA to stop SCC from selling its chips. SCC ultimately succeeded on appeal, but only after 19 months of expensive litigation while its product was held off the market.
- Microsoft used the DMCA to try to shut down competition for gaming accessories. Datel, Inc. produces third-party accessories for every major videogame console, including Microsoft’s Xbox 360. Microsoft issued a mandatory firmware update for all Xbox 360 consoles connected to the Internet: this update had no effect on Microsoft’s own memory cards, but rendered Datel’s less expensive memory cards completely unusable. When Datel sued Microsoft for antitrust violations, Microsoft counterclaimed by accusing Datel of violating the DMCA. In a nutshell, Microsoft forced consumers to purchase its own memory cards and then used the DMCA to attack legitimate competitors.
- Calculator manufacturers have brought circumvention claims against hobbyists who reverse-engineered their personal graphing calculators to develop alternative operating systems for personal use.
1201 reform is also long overdue. Here, again, Rep. Zoe Lofgren has stepped up. Her “Unlocking Technology Act,” would rewrite the definition of "circumvention" under Section 1201 to include only circumvention that infringes or facilitates the infringement of copyright. IN other words, if you are trying to do something otherwise legal, the fact that you have to break a lock to do it shouldn’t put you at legal risk.
End User License Agreements
Traditionally, once a person has purchased a product, they have been free to use it pretty much however they see fit, spurring hobbyists, tinkers, and repairpersons alike. Purchasers have also been free to use competitors’ add-on software and hardware that interoperate with the goods they buy, because innovators have been able to develop and distribute such technologies.
That expectation is upended when it comes to products that come with embedded software, from tractors to refrigerators to toasters and children’s toys. Software is supposed to make our stuff smarter, but it also makes “our” stuff not really “ours.” We own the hardware, but supposedly we only license the software in it. And those licensing agreements often impose conditions on your use of the product, including:
- Forbidding the use of “unauthorized” hardware or software in conjunction with the device, including plugs, dongles, and other peripherals that we need to make the devices work or work better.
- Forbidding second-hand sale of a used device; and
- Requiring the user to agree to ever more onerous EULAs to continue using their device at all.
Users who violate these terms can find themselves threatened with a copyright lawsuit, but that is relatively rare. Instead, a more common tactic is to threaten third parties who want to offer add-on products or services (including repair) that might conflict with the EULA terms – inhibiting competition and giving vendor outsized control over innovation, repair, privacy, and security. Suddenly, the purchase of a toaster creates an ongoing relationship between the purchaser and the manufacturer – like it or not – and the prospect that your toaster will stop working if the manufacturer doesn’t like how you repair it.
Studies suggest that most customers have no idea they are “agreeing” to such terms. But even if they do, they have few options short of refusing to buy the device. And courts have been far too willing to uphold such terms, even when the record is clear that no one has read them or even explicitly agreed to the terms, and even when they prevent users from doing what they want with a device that they paid for.
Given that courts have done such a poor job of scrutinizing these one-sided contracts, legislators should step in. Congress could help prevent these anticompetitive effects by forbidding waiver of fair use rights except in fully negotiated contracts. And state legislatures could pass a law holding any such waivers contradict public policy (clearing the way for lawsuits under state unfair competition laws.)
Creating competition in the digital world isn’t rocket science. It does, however, require us to take a hard look at the assumptions we’ve made about how laws and technology actually work in practice and adjust so that we have a level playing field not only for all competitors, but between sellers and users of technology. Changing the impact of the CFAA, DMCA 1201 and EULA law are three ways we can help restore the balance.