Phishing in the Time of COVID-19: How to Recognize Malicious Coronavirus Phishing Scams
Update 3-26-20: A new prevalent example of Android Spyware that leverages COVID-19 as a way to deliver their malicious product has been reported by researchers at Lookout. This particular malware, called "corona live 1.1.", comes out of Libya and seems to mostly be targeting Libyan citizens. Like other examples...
How Ring Could Really Protect Its Users: Encrypt Footage End-To-End
Ring Doorbell App Packed with Third-Party Trackers
Ring isn't just a product that allows users to surveil their neighbors. The company also uses it to surveil its customers.An investigation by EFF of the Ring doorbell app for Android found it to be packed with third-party trackers sending out a plethora of customers’ personally identifiable information (PII). Four...
Why Adding Client-Side Scanning Breaks End-To-End Encryption
Recent attacks on encryption have diverged. On the one hand, we’ve seen Attorney General William Barr call for “lawful access” to encrypted communications, using arguments that have barely changed since the 1990’s. But we’ve also seen suggestions from a different set of actors for more purportedly “reasonable” interventions,...
Phony HTTPS Everywhere Extension Used in Fake Tor Browser
ESET researchers recently discovered a false “trojanized” version of Tor Browser that collectively stole $40,000 USD in Bitcoin.This does not mean that Tor or Tor Browser itself is compromised in any way. It only means that attackers found a new, insidious way to create and distribute a fake...
Why Fiber is Vastly Superior to Cable and 5G
The United States, its states, and its local governments are in dire need of universal fiber plans. Major telecom carriers such as AT&T and Verizon have discontinued their fiber-to-the-home efforts, leaving most people facing expensive cable monopolies for the future. While much of the Internet infrastructure has already transitioned...
Encrypted DNS Could Help Close the Biggest Privacy Gap on the Internet. Why Are Some Groups Fighting Against It?
Thanks to the success of projects like Let’s Encrypt and recent UX changes in the browsers, most page-loads are now encrypted with TLS. But DNS, the system that looks up a site’s IP address when you type the site’s name into your browser, remains unprotected by encryption.Because of...
Watering Holes and Million Dollar Dissidents: the Changing Economics of Digital Surveillance
Recently, Google’s Project Zero published a report describing a newly-discovered campaign of surveillance using chains of zero day iOS exploits to spy on iPhones. This campaign employed multiple compromised websites in what is known as a “watering hole” attack. The compromised websites would automatically run the chain of exploits...
Human Rights Watch Reverse-Engineers Mass Surveillance App Used by Police in Xinjiang
For years, Xinjiang has been a testbed for the Chinese government’s novel digital and physical surveillance tactics, as well as human rights abuses. But there is still a lot that the international human rights community doesn’t know, especially when it comes to post-2016 Xinjiang. Last Wednesday, Human Rights Watch...
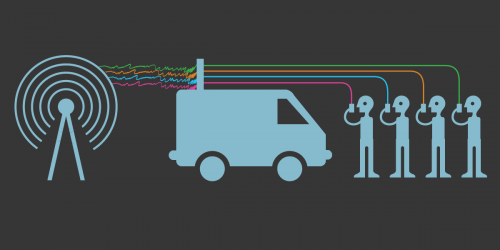
The 5G Protocol May Still Be Vulnerable to IMSI Catchers
It’s hard to talk about the vulnerabilities in cellular technology without increasing the amount of fear, uncertainty, and doubt. There is already much uncertainty around cell-site simulators (CSS, aka Stingrays), their capabilities, and how widely they are used. Partly this is because of the veil of secrecy that has...