Illinois has joined the growing ranks of states limiting how police may use cell-site simulators, invasive technology devices that masquerade as cell phone towers and turn our mobile phones into surveillance devices. By adopting the Citizen Privacy Protection Act, Illinois last month joined half a dozen other states—as well as the Justice Department and one federal judge—that have reiterated the constitutional requirement for police to obtain a judicial warrant before collecting people's location and other personal information using cell-site simulators.
Recognizing how invasive the latest versions of IMSI-catchers can be, legislators in Illinois authorized police to use cell-site simulators in only two ways.
By going beyond a warrant requirement and prohibiting police from intercepting data and voice transmissions or conducting offensive attacks on personal devices, the Illinois law establishes a new high watermark in the battle to prevent surveillance technology from undermining civil liberties. Illinois also set an example for other states to follow by providing a powerful remedy when police violate the new law by using a cell-site simulator without a warrant: wrongfully collected information is inadmissible in court, whether to support criminal prosecution or any other government proceedings.
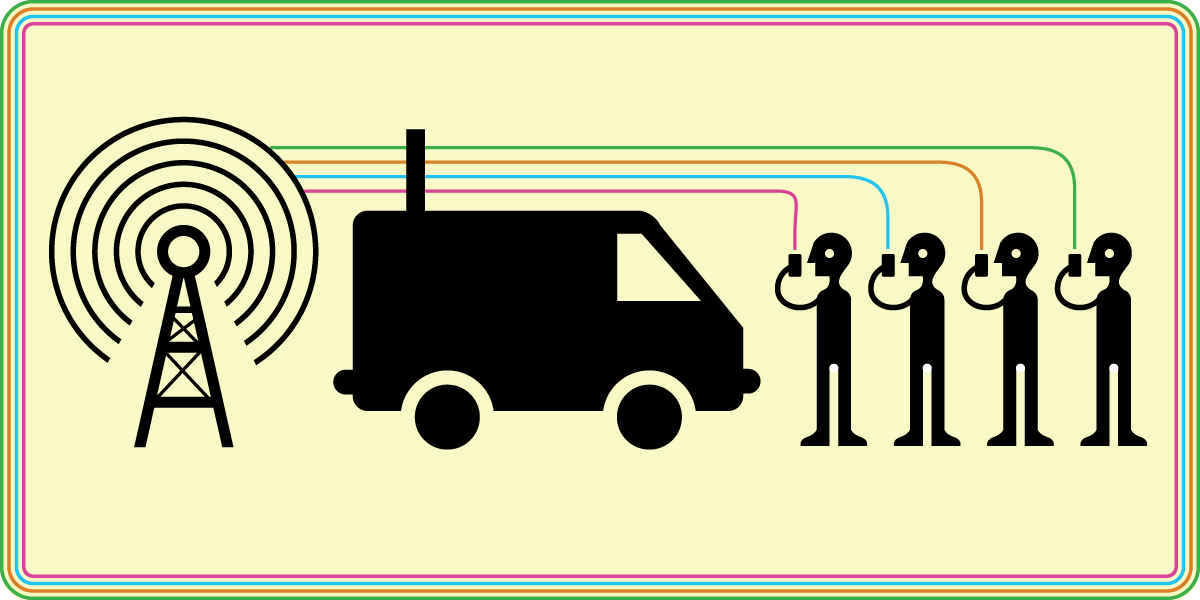
Tools to monitor cell phones
Cell-site simulators are sometimes called “IMSI catchers” because they seize from every cell phone within a particular area its unique International Mobile Subscriber Identity, and force those phones to connect to them, instead of real cell towers.
Early versions of the devices—such as the Stingray device used by police in major U.S. cities since at least 2007 after having been used by federal authorities since at least the 1990s—were limited to location tracking, as well as capturing and recording data and voice traffic transmitted by phones. Later versions, however, added further capabilities which policymakers in Illinois have become the first to address.
Cell phone surveillance tools have eroded constitutional rights guaranteed under the Fourth Amendment’s protection from unreasonable searches and seizures in, at minimum, tens of thousands of cases. Stingrays were deployed thousands of times in New York City alone—and even more often in Baltimore—without legislative or judicial oversight, until in 2011 a jailhouse lawyer accused of tax fraud discovered the first known reference to a “Stingray” in court documents relating to the 2008 investigation that led to his arrest and conviction.
Meanwhile, government and corporate secrecy surrounding police uses of Stingrays has undermined Fifth and Sixth Amendment rights to due process, such as the right to challenge evidence used by one’s accusers. Contracts with police departments demanded by corporate device manufacturers imposed secrecy so severe that prosecutors walked away from legitimate cases across the country rather than risk revealing Stingrays to judges by pursuing prosecutions based on Stingray-collected evidence.
Citing the constraint of a corporate non-disclosure agreement, a police officer in Baltimore even risked contempt charges by refusing to answer judicial inquiries about how police used the devices. Baltimore public defender Deborah Levi explains, “They engage in a third-party contract to violate people’s constitutional rights.”
Several states agree: Get a warrant
In one respect, Illinois is walking well-settled ground.
By requiring that state and local police agents first seek and secure a judicial order based on individualized probable cause of criminal misconduct before using a cell-site simulator, Illinois has joined half a dozen other states (including California, Washington, Utah, Minnesota, and Virginia) that have already paved that road.
At the federal level, the Justice Department took action in 2015 to require federal agencies to seek warrants before using the devices. And just two weeks before Illinois enacted its new law, a federal judge in New York ruled for the first time that defendants could exclude from trial evidence collected from an IMSI-catcher device by police who failed to first obtain a judicial order.
These decisions vindicate core constitutional rights, as well as the separation of powers and underscore that warrants are constitutionally crucial.
It's true that warrants are not particularly difficult for police to obtain when based on legitimate reasons for suspicion. When New York Court of Appeals Chief Judge Sol Wachtler observed in 1985 that any prosecutor could persuade a grand jury to “indict a ham sandwich,” he was talking about the ease with which the government can satisfy the limited scrutiny applied in any one-sided process, including that through which police routinely secure search warrants.
But while judicial warrants do not present a burdensome constraint on legitimate police searches, they play an important role in the investigative process. Warrantless searches are conducted essentially by fiat, without independent review, and potentially arbitrarily. Searches conducted pursuant to a warrant, however, bear the stamp of impartial judicial review and approval.
Warrants ensure, for instance, that agencies do not treat their public safety mandate as an excuse to pursue personal vendettas, or the kinds of stalking “LOVEINT” abuses to which NSA agents and contractors have occasionally admitted. Requiring authorization from a neutral magistrate, put simply, maintains civilian control over police.
Despite its importance and ease for authorities to satisfy, the warrant requirement has ironically suffered frequent erosion by the courts—making all the more important efforts by states like Illinois to legislatively reiterate and expand it.
But in two important respects beyond the warrant requirement, the Illinois Citizen Privacy Protection Act breaks new ground.
Breaking new ground: Allowing an exclusionary remedy
First, the Illinois law is the first policy of its kind in the country that carries a price for law enforcement agencies that violate the warrant requirement. If police use a cell-site simulator to gather information without securing a judicial order, then courts will suppress that information and exclude it from any consideration at trial.
This vindicates the rights of accused individuals by enabling them to exclude illegally collected evidence. It also helps ensure that police use their powerful authorities for only legitimate reasons based on probable cause to suspect criminal activity, rather than fishing expeditions without real proof of misconduct, or for that matter, the personal, racial, or financial biases of police officers.
Like the warrant requirement created to limit the powers of police agencies, the exclusionary rule on which the judiciary relies to enforce the warrant requirement has endured doctrinal erosion over the past generation. Courts have allowed one exception after another, allowing prosecutors to use “fruits of the poisonous tree” in criminal trials despite violations of constitutional rights committed by police when collecting them.
In this context, the new statute in Illinois represents a crucial public policy choice explicitly extending the critical protections of the warrant requirement and exclusionary rule.
Breaking new ground: Prohibiting offensive uses
The new Illinois law also limits the purposes for which cell-site simulators may be used, even pursuant to a judicial order. It flatly prohibits several particularly offensive uses that remain largely overlooked elsewhere.
When Stingrays (and their frequent secret use by local police departments across the country) first attracted attention, most concerns addressed the location tracking capabilities of the device’s first generation, obtained by domestic police departments as early as 2003.
But while Stingrays presented profound constitutional concerns 10 years ago, they present even greater concerns now, because of technology advancements in the past decade enabling stronger surveillance and even militaristic offensive capabilities. Unlike early versions of the devices that could be used only for location monitoring or gathering metadata, later versions, such as the Triggerfish, Hailstorm and Stargrazer series, can be used to intercept voice communications or browsing history in real-time, mount offensive denial of service attacks on a phone, or even plant malware on a device.
Recognizing how invasive the latest versions of IMSI-catchers can be, legislators in Illinois authorized police to use cell-site simulators in only two ways: after obtaining a warrant, police may use the devices to locate or track a known device, or instead to identify an unknown device.
Even if supported by a judicial order, the Citizen Privacy Protection Act affirmatively bans all other uses of these devices. Prohibited activities include intercepting the content or metadata of phone calls or text messages, planting malware on someone’s phone, or blocking a device from communicating with other devices.
The use limitations enshrined in Illinois law are among the first of their kind in the country.
The Illinois statute also requires police to delete any data (within 24 hours after location tracking, or within 72 hours of identifying a device) incidentally obtained from third parties, such as non-targets whose devices are forced to connect to a cell-site simulator. These requirements are similar to those announced by a federal magistrate judge in Illinois who in November 2015 imposed on a federal drug investigation minimization requirements including an order to “immediately destroy all data other than the data identifying the cell phone used by the target. The destruction must occur within forty-eight hours after the data is captured.”
Enhancing security through transparency
Beyond enforcing constitutional limits on the powers of law enforcement agencies, and protecting individual rights at stake, the new law in Illinois also appropriately responds to an era of executive secrecy.
The secrecy surrounding law enforcement uses of IMSI-catchers has also compromised security. As the ACLU’s Chris Soghoian has explained alongside Stephanie Pell from West Point’s Army Cyber Institute and Stanford University, “the general threat that [any particular] technology poses to the security of cellular networks” could outweigh its “increasing general availability at decreasing prices.” With respect to cell-site simulators, in particular:
[C]ellular interception capabilities and technology have become, for better or worse, globalized and democratized, placing Americans’ cellular communications at risk of interception from foreign governments, criminals, the tabloid press and virtually anyone else with sufficient motive to capture cellular content in transmission. Notwithstanding this risk, US government agencies continue to treat practically everything about this cellular interception technology, as a closely guarded, necessarily secret “source and method,” shrouding the technical capabilities and limitations of the equipment from public discussion….
Given the persistent secrecy surrounding IMSI-catchers and the unknown risks they pose to both individual privacy and network security, the statutory model adopted by Illinois represents a milestone not only for civil liberties but also for the security of our technological devices. Khadine Bennett from the ACLU of Illinois explained the new law’s importance in terms of the secrecy pervading how police have used cell-site simulators:
For so long, uses of IMSI-catchers such as Stingrays have been behind the scenes, enabling searches like the pat down of thousands of cell phones at once without the users ever even knowing it happened. It’s exciting to see Illinois adopt a measure to ensure that these devices are used responsibly and appropriately, and I hope to see more like it emerge around the country.
EFF enthusiastically agrees with Ms. Bennett. If you’d like to see the Citizen Privacy Protection Act’s groundbreaking requirements adopted in your state, you can find support through the Electronic Frontier Alliance.










