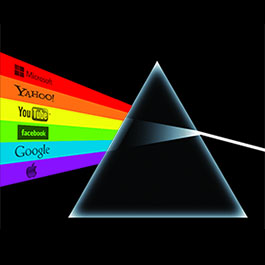
A lot remains uncertain about the number of users affected by the NSA PRISM surveillance program that is taking place, the extent to which companies are involved, and how the NSA handles this sensitive data. Does the NSA regularly collect and examine a huge swath of the cloud communications of American and foreign Internet users? Does the agency present evidence and seek careful judicial review to obtain limited amounts of user data related to individual investigations? Or is the answer somewhere in the middle, with queries being constructed such that algorithms scan most or all of the accounts, identifying a smaller set of "interesting" accounts whose contents are sent to the NSA?
This post attempts to set out some fundamental questions that we need answered in order to gain enough clarity on the surveillance taking place to have an informed democratic policy debate.1 We also give our approximations of the realistic "Best case" and "Worst case" scenarios given what we already know about the program, to highlight the range of possible realities.
For each company involved, how many user accounts have had some private data transmitted to the NSA? [+]
While companies have denied giving the NSA "direct access" to their servers, those denials have been carefully worded and the companies have admitted that they do comply with what they consider to be lawful orders — especially 702 FISA orders2 — and push back if these orders are too broad. The New York Times reported that some of these orders can be "a broad sweep for intelligence, like logs of certain search terms." Unfortunately, without more specificity from companies detailing the approximate number of user accounts whose data is touched by such orders, we are left in the dark about exactly how broad the orders are.
Could the NSA, for example, ask for all Gmail emails that contain the word “golden gate bridge” that were sent or received in the last 24 hours? For all private Facebook messages of any user that signed up through an IP address associated with a particular country over a one month period? Are there orders for information which has to be provided on an ongoing basis? Is information filtered by the companies so that no information on Americans is handed over? In order to have a better grasp of the scope, we have been encouraging companies to provide more granular information in their transparency reports or elsewhere.
We're pleased to see requests from Google and Facebook to the government for more leeway to publish this information in transparency reports. These requests should be taken seriously, and we also encourage the NSA to itself be more forthright with what information is collected.
Best case: The NSA sends a small number FISA 702 orders that are narrowly targeted for specific investigations and touch upon only a small number of user accounts; ideally at most hundreds or perhaps thousands of accounts have information passed on to the NSA every year.
Worst case: Companies receive incredibly broad FISA 702 orders that result in turning over huge swaths of user data to the NSA on a regular or ongoing basis, such as the emails of all users in a particular country, or any that contain a phrase like “golden gate bridge”.
What information about users' activities is being collected without the cooperation of companies? [+]
There is a lot we do not know about what the NSA can collect without the cooperation of companies. While entities like the NSA are in a position to gather some forms of metadata without involving a company, the encryption deployed by companies such as Google and Facebook in recent years makes it hard for the NSA to obtain content without involving companies. Still, one interpretation of PRISM is that the NSA is using aggressive tactics like stealing private encryption keys from company servers in order to conduct spying without company knowledge. Alex Stamos has provided a taxonomy of possibilities that technically knowledgeable users may find useful in understanding the array of possibilities.
Best case: The NSA is not monitoring any metadata or content data of users except via lawful and targeted requests made to the companies.
Worst case: The NSA is broadly monitoring user metadata and content data without any company involvement.
What internal checks does the NSA have on how data is requested and (mis)used? [+]
Right now we know extremely little about how the NSA uses the data. We know that it is used for "national security" purposes such as espionage, national security investigations, and tracking nuclear proliferation. It is safe to assume that US spy agencies monitor and intervene in business activities (one example) as well as the affairs of other states, probably including the politics of democracies (one possible example). But we don't know how frequently such targets might be chosen, or what standards the US intelligence community might apply to those activities.
Aside from purposes, there are other important questions about checks and balances. What evidentiary standard is required for information to be obtained from companies? Once this collection occurs but before a person looks at the data, what minimization procedures take place to ensure that only appropriately targeted data is examined by analysts? Is data deleted, and if so what triggers deletion? What percentage of data is deleted? Is data about Americans always deleted once it is discovered? For people employed at the NSA in a position to look at very private information such as the content of a personal email, what checks are there to prevent that person from misusing this information?
Best case: Data is only sought once there is substantial evidence of terrorism of other activities that might affect national security. Only data relevant to an active investigation is stored, and only as long as it is needed. Data that is not relevant is immediately deleted. All employee access of private data is logged and regularly reviewed for inappropriate or questionable uses.
Worst case: Analysts can go on fishing expeditions without any evidence of wrongdoing. Data is stored indefinitely. Irrelevant data is not discarded, including domestic data on American users. There are few checks on how employees with access can use the tools at their disposal, and little accountability as a result.
America has long struggled to reconcile democratic principles with intelligence imperatives. Striking the right balance is difficult; while there may be legitimate arguments for confidentiality with respect to specific sources and operations, secret legal interpretations and practices are plainly antithetical to American values: the public, acting through Congress, gets to decide what's allowed. That critical governance process is only possible with transparency. Implausible and unsubstantiated claims that oversight endangers national security only further erode the American public's trust in the intelligence community. We hope that the NSA will choose a better path: appropriately declassify information, work with companies to disclose the scope of their surveillance programs, and earn the trust of the American public. We urge you to join us in asking the hard questions.
- 1. Note that the following questions are about the sources for the collection of information, and the scope of that collection, but aren't centered around “PRISM” itself to avoid the word games that government and intelligence agency officials have played to avoid giving substantive answers about the surveillance taking place.
- 2. FISA 702 orders refer to 50 USC § 1881a.