It’s been one year since the Guardian first published the Foreign Intelligence Surveillance Court order, leaked by former NSA contractor Edward Snowden, that demonstrated that the NSA was conducting dragnet surveillance on millions of innocent people. Since then, the onslaught of disturbing revelations, from disclosures, admissions from government officials, Freedom of Information Act requests, and lawsuits, has been nonstop. On the anniversary of that first leak, here are 65 things we know about NSA spying that we did not know a year ago:
1. We saw an example of the court orders that authorize the NSA to collect virtually every phone call record in the United States—that’s who you call, who calls you, when, for how long, and sometimes where.
2. We saw NSA Powerpoint slides documenting how the NSA conducts “upstream” collection, gathering intelligence information directly from the infrastructure of telecommunications providers.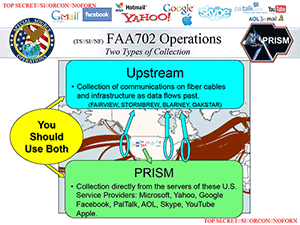
3. The NSA has created a “content dragnet” by asserting that it can intercept not only communications where a target is a party to a communication but also communications “about a target, even if the target isn’t a party to the communication.”
4. The NSA has confirmed that it is searching data collected under Section 702 of the FISA Amendments Act to access American’s communications without a warrant, in what Senator Ron Wyden called the "back door search loophole."
5. Although the NSA has repeatedly stated it does not target Americans, its own documents show that searches of data collected under Section 702 are designed simply to determine with 51 percent confidence a target’s “foreignness.’”
6. If the NSA does not determine a target’s foreignness, it will not stop spying on that target. Instead the NSA will presume that target to be foreign unless they “can be positively identified as a United States person.”
7. A leaked internal NSA audit detailed 2,776 violations of rules or court orders in just a one-year period.
8. Hackers at the NSA target sysadmins, regardless of the fact that these sysadmins themselves may be completely innocent of any wrongdoing.
 9. The NSA and CIA infiltrated games and online communities like World of Warcraft and Second Life to gather data and conduct surveillance.
9. The NSA and CIA infiltrated games and online communities like World of Warcraft and Second Life to gather data and conduct surveillance.
10. The government has destroyed evidence in EFF’s cases against NSA spying. This is incredibly ironic, considering that the government has also claimed EFF’s clients need this evidence to prove standing.
11. Director of National Intelligence James Clapper lied to Congress when asked directly by Sen. Ron Wyden whether the NSA was gathering any sort of data on millions of Americans.
12. Microsoft, like other companies, has cooperated closely with the FBI to allow the NSA to “circumvent its encryption and gain access to users’ data.”
13. The intelligence budget in 2013 alone was $52.6 billion— this number was revealed by a leaked document, not by the government. Of that budget, $10.8 billion went to the NSA. That’s approximately $167 per person in the United States.
14. The Foreign Intelligence Surveillance Court has issued orders that allow the NSA to share raw data—without personally identifying information stripped out— with the FBI, CIA, and the National Counterterrorism Center.
15. Pursuant to a memorandum of understanding, the NSA regularly shares raw data with Israel without stripping out personally identifying information about U.S. persons.
16. The Snowden disclosures have made it clear the Obama administration misled the Supreme Court about key issues in ACLU’s case against NSA spying, Clapper v. Amnesty International, leading to the dismissal of the case for lack of standing.
17. The NSA “hacked into Al Jazeera's internal communications system.” NSA documents stated that “selected targets had ‘high potential as sources of intelligence.’”
18. The NSA used supposedly anonymous Google cookies as beacons for surveillance, helping them to track individual users.
 19. The NSA “intercepts ‘millions of images per day’ — including about 55,000 ‘facial recognition quality images’” and processes them with powerful facial recognition software.
19. The NSA “intercepts ‘millions of images per day’ — including about 55,000 ‘facial recognition quality images’” and processes them with powerful facial recognition software.
20. The NSA facial recognition program “can now compare spy satellite photographs with intercepted personal photographs taken outdoors to determine the location.”
21. Although most NSA reform has focused on Section 215 of the PATRIOT Act, and most advocates have also pushed for reform of Section 702 of the FISA Amendments Act, some of the worst NSA spying happens under the authority of Executive Order 12333, which President Obama could repeal or modify today.
22. The NSA collected Americans’ cell phone location information for two years as part of a pilot project to see how it could use such information in its massive databases.
23. In one month, March 2013, the NSA collected 97 billion pieces of intelligence from computer networks worldwide, including 3 billion pieces of intelligence from US computer networks.
 24. The NSA has targeted Tor, a set of tools that allow Internet users to browse the net anonymously.
24. The NSA has targeted Tor, a set of tools that allow Internet users to browse the net anonymously.
25. The NSA program MUSCULAR infiltrates links between the global data centers of technology companies such as Google and Yahoo. Many companies have responded to MUSCULAR by encrypting traffic over their internal networks.
26. The XKEYSCORE program analyzes emails, online chats and the browsing histories of millions of individuals anywhere in the world.
27. NSA undermines the encryption tools relied upon by ordinary users, companies, financial institutions, targets, and non-targets as part of BULLRUN, an unparalleled effort to weaken the security of all Internet users, including you.
28. The NSA’s Dishfire operation has collected 200 million text messages daily from users around the globe, which can be used to extract valuable information such as location data, contact retrievals, credit card details, missed call alerts, roaming alerts (which indicate border crossings), electronic business cards, credit card payment notifications, travel itinerary alerts, and meeting information.
29. Under the CO-TRAVELER operation, the US collects location information from global cell towers, Wi-Fi, and GPS hubs, which is then information analyzed over time, in part in order to determine a target’s traveling companions.
30. A 2004 memo entitled “DEA- The ‘Other’ Warfighter”, states that the DEA and NSA “enjoy a vibrant two-way information-sharing relationship.”
31. When the DEA acts on information its Special Operations Division receives from the NSA, it cloaks the source of the information through “parallel construction,” going through the charade of recreating an imaginary investigation to hide the source of the tip, not only from the defendant, but from the court. This was intended to ensure that no court rules on the legality or scope of how NSA data is used in ordinary investigations.
32. The fruits of NSA surveillance routinely end up in the hands of the IRS. Like the DEA, the IRS uses parallel construction to cloak the source of the tip.
33. Even the President’s handpicked Privacy and Civil Liberties Oversight Board recommended that the government end Section 215 mass telephone records collection, because that collection is ineffective, illegal, and likely unconstitutional.
34. The NSA has plans to infect potentially millions of computers with malware implants as part of its Tailored Access Operations.
35. The NSA had a secret $10 million contract with security firm RSA to create a “back door” in the company’s widely used encryption products.
36. The NSA tracked access to porn and gathered other sexually explicit information “as part of a proposed plan to harm the reputations of those whom the agency believes are radicalizing others through incendiary speeches.”
37. The NSA and its partners exploited mobile apps, such as the popular Angry Birds game, to access users’ private information such as location, home address, gender, and more.
38. The Washington Post revealed that the NSA harvests “hundreds of millions of contact lists from personal e-mail and instant messaging accounts around the world, many of them belonging to Americans.”
Many of the Snowden revelations have concerned the NSA’s activities overseas, as well as the activities of some of the NSA’s closest allies, such as the its UK counterpart GCHQ. Some of these have been cooperative ventures. In particular, the “Five Eyes”— The United States, New Zealand, Australia, the United Kingdom, and Canada— share citizen data amongst themselves - providing loopholes that might undermine national legislation.
39. The NSA paid its British counterpart GCHQ $155 million over the last three years “to secure access to and influence over Britain's intelligence gathering programmes.”
40. The Guardian reported: “In one six-month period in 2008 alone, [GCHQ] collected webcam imagery – including substantial quantities of sexually explicit communications – from more than 1.8-million Yahoo user accounts globally.”
41. GCHQ used malware to compromise networks belonging to the Belgian telecommunications company Belgacom.
42. Major telecommunications companies including BT, Vodafone, and Verizon business have given GCHQ unlimited access to their fiberoptic cables
43. GCHQ used DDoS attacks and other methods to interrupt Anonymous and LulzSec communications, including communications of people not charged with any crime.
44. GCHQ’s Bude station monitored leaders from the EU, Germany, and Israel. It also targeted non-governmental organizations such as Doctors of the World.
45. The NSA’s partners Down Under, the Australian Signals Directorate, has been implicated in breaches of attorney-client privileged communications, undermining a foundational principle of our shared criminal justice system.
46. Australian intelligence officials spied on the cell phones of Indonesian cabinet ministers and President Susilo Bambang.
47. In 2008, Australia offered to share its citizens’ raw information with intelligence partners.
48. CSEC helped the NSA spy on political officials during the G20 meeting in Canada.
49. CSEC and CSIS were recently rebuked by a federal court judge for misleading him in a warrant application five years ago with respect to their use of Five Eyes resources in order to track Canadians abroad.
Ironically, some of the NSA’s operations have been targeted at countries that have worked directly with the agency in other instances. And some simply seemed unnecessary and disproportionate.
50. NSA documents show that not all governments are clear about their own level of cooperation with the NSA. As the Intercept reports, “Few, if any, elected leaders have any knowledge of the surveillance.”
51. The NSA is intercepting, recording, and archiving every single cell phone call in the Bahamas.
52. The NSA monitored phone calls of at least 35 world leaders.
53. The NSA spied on French diplomats in Washington and at the UN.
54. The NSA hacked in to Chinese company Huawei's networks and stole its source code.
55. The NSA bugged EU embassies in both New York and Washington. It copied hard drives from the New York office of the EU, and tapped the internal computer network from the Washington embassies.
56. The NSA collected the metadata of more than 45-million Italian phone calls over a 30 day period. It also maintained monitoring sites in Rome and Milan.
57. The NSA stored data from approximately 500-million German communications connections per month.
58. The NSA collected data from over-60 million Spanish telephone calls over a 30-day period in late 2012 and early 2013 and spied on members of the Spanish government.
59. The NSA collected data from over 70-million French telephone calls over a 30-day period in late 2012 and early 2013.
60. The Hindu reported that, based on NSA documents: “In the overall list of countries spied on by NSA programs, India stands at fifth place.”
61. The NSA hacked into former Mexican President Felipe Calderon’s official email account.
62. The Guardian reported: “The NSA has, for years, systematically tapped into the Brazilian telecommunication network and indiscriminately intercepted, collected and stored the email and telephone records of millions of Brazilians.”
63. The NSA monitored emails (link in Portuguese), telephone calls, and text messages of Brazilian President Dilma Roussef and her top aides.
64. Germany’s intelligence agencies cooperated with the NSA and implemented the NSA’s XKeyscore program, while NSA was in turn spying on German leaders.
65. Norwegian daily Dagbladet reported (Link in Norwegian) that the NSA acquired data on 33 million Norwegian cell phone calls in one 30-day period.”
There’s no question that the international relationships Obama pledged to repair, as well as the confidence of the American people in their privacy and constitutional rights, have been damaged by the NSAs dragnet surveillance. But one year later, both the United States and international governments have not taken the steps necessary to ensure that this surveillance ends. That’s why everyone must take action— contact your elected representative, join Reset the Net, and learn about how international law applies to U.S. surveillance today.