Recognizing the year’s worst in government transparency
The cause of government transparency finally broke through to the popular zeitgeist this year. It wasn’t an investigative journalism exposé or a civil rights lawsuit that did it, but a light-hearted sitcom about a Taiwanese American family set in Orlando, Florida, in the late 1990s.
In a January episode of ABC’s Fresh Off the Boat, the Huang family’s two youngest children—overachievers Evan and Emery—decide if they sprint on all their homework, they’ll have time to plan their father’s birthday party.
“Like the time we knocked out two English papers, a science experiment, and built the White House out of sugar cubes,” Evan said. “It opened up our Sunday for filing Freedom of Information requests.”
“They may not have figured out who shot JFK,” Emery added. “But we will.”
The eldest child, teenage slacker Eddie, concluded with a sage nod, “You know, once in a while, it’s good to know nerds.”
Amen to that. Around the world, nerds of all ages are using laws like the United States’ Freedom of Information Act (and state-level equivalent laws) to pry free secrets and expose the inner workings of our democracy. Each year, open government advocates celebrate these heroes during Sunshine Week, an annual advocacy campaign on transparency.
But the journalists and researchers who rely on these important measures every day can’t help but smirk at the boys’ scripted innocence. Too often, government officials will devise novel and outrageous ways to reject requests for information or otherwise stymie the public’s right to know. Even today—20 years after the events set in the episode—the White House continues to withhold key documents from the Kennedy assassination files.
Since 2015, the Electronic Frontier Foundation (a nonprofit that advocates for free speech, privacy and government transparency in the digital age) has published The Foilies to recognize the bad actors who attempted to thwart the quests for truth of today’s Evans and Emerys. With these tongue-in-cheek awards, we call out attempts to block transparency, retaliation against those who exercise their rights to information, and the most ridiculous examples of incompetence by government officials who handle these public records.
- The Corporate Eclipse Award - Google, Amazon, and Facebook
- The Unnecessary Box Set Award - Central Intelligence Agency
- The (Harlem) Shaky Grounds for Redaction Award - Federal Communications Commission
- The Unreliable Narrator Award - President Donald Trump, the U.S. Department of Justice and U.S. District Court Judges
- The Cross-Contamination Award - Stanford Law Professor Daniel Ho
- The Scanner Darkly Award - St. Joseph County Superior Court
- The Cash for Crash Award - Michigan State Police
- The Bartering with Extremists Award - California Highway Patrol
- The Preemptive Shredding Award - Inglewood Police Department
- The What the Swat? Award - Nova Scotia and Halifax Law Enforcement
- The Outrageous Fee Request of the Year - City of Seattle
- The Intern Art Project Award - Vermont Gov. Phil Scott
- The Least Transparent Employer Award - U.S. Department of Justice
- The Clawback Award - The Broward County School Board
- The Wrong Way to Plug a Leak Award - City of Greenfield, California
- If it Looks like a Duck Award - Brigham Young University Police
- The Insecure Security Check Award - U.S. Postal Service
The Corporate Eclipse Award - Google, Amazon, and Facebook
Sunshine laws? Tech giants think they can just blot those out with secretive contracts. But two nonprofit groups—Working Partnerships and the First Amendment Coalition—are fighting this practice in California by suing the city of San Jose over an agreement with Google that prevents city officials from sharing the public impacts of development deals, circumventing the California Public Records Act.
Google’s proposed San Jose campus is poised to have a major effect on the city’s infrastructure, Bloomberg reported. Yet, according to the organization’s lawsuit, records analyzing issues of public importance such as traffic impacts and environmental compliance were among the sorts of discussions Google demanded be made private under their non-disclosure agreements.
And it’s not just Google using these tactics. An agreement between Amazon and Virginia includes a provision that the state will give the corporate giant—which is placing a major campus in the state—a heads-up when anyone files a public records request asking for information about them. The Columbia Journalism Review reported Facebook has also used this increasingly common strategy for companies to keep cities quiet and the public in the dark about major construction projects.
The Unnecessary Box Set Award - Central Intelligence Agency
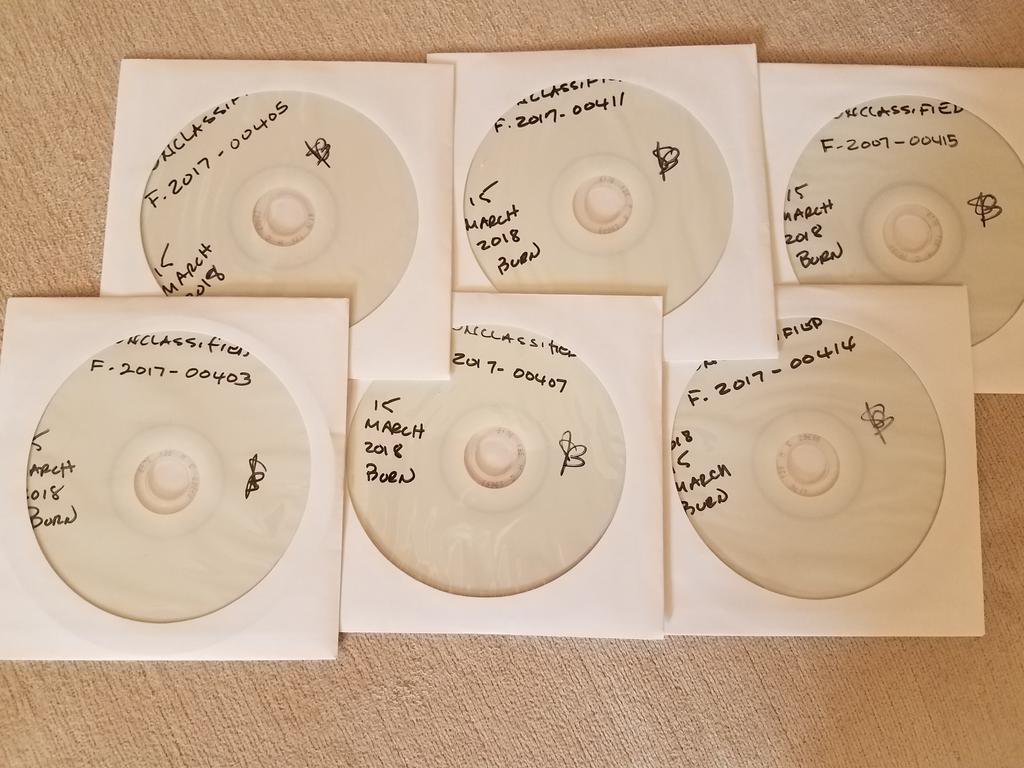
Courtesy of National Security Counselors
After suing the CIA to get access to information about Trump’s classified briefings, Kel McClanahan of National Security Counselors was expecting the agency to send over eight agreed-upon documents.
What he was not expecting was for the files—each between three and nine pages each—-to be spread out across six separate CD-ROMs, each burned within minutes of each other, making for perhaps the most unnecessary box set in the history of the compact disc.
What makes this “extra silly,” McClanahan said, is that the CIA has previously complained about how burdensome and costly fulfilling requests can be. Yet the CIA could have easily combined several requests onto the same disc and saved themselves some time and resources. After all, a a standard CD-ROM can hold 700 MB, and all of the files took only 304 KB of space.
The (Harlem) Shaky Grounds for Redaction Award - Federal Communications Commission

After repealing the Open Internet Order and ending net neutrality, Federal Communications Commission Chairman Ajit Pai doubled down on his efforts to ruin online culture. He released a cringe-inducing YouTube video titled “7 Things You Can Still Do on the Internet After Net Neutrality" that featured his own rendition of the infamous “Harlem Shake” meme. (For the uninitiated, the meme is characterized by one person subtly dancing in a room of people to Baauer’s track “Harlem Shake.” Then the bass drops and the crowd goes nuts, often with many people in costumes.)
Muckrock editor JPat Brown filed a Freedom of Information Act request for emails related to the video, but the FCC rejected the request, claiming the communications were protected “deliberative” records.
Brown appealed the decision, and the FCC responded by releasing all the email headers, while redacting the contents, claiming that anything more would cause “foreseeable harm.” Brown did not relent, and a year later the FCC capitulated and released the unredacted emails.
“So, what did these emails contain that was so potentially damaging that it was worth risking a potential FOIA lawsuit over?” Brown writes. “Pai was curious when it was going live, and the FCC wanted to maintain a veto power over the video if they didn’t like it.” The most ridiculous redaction of all was a tiny black box in an email from the FCC media director. Once removed, all that was revealed was a single word: “OK.”
The Unreliable Narrator Award - President Donald Trump, the U.S. Department of Justice and U.S. District Court Judges
When President Trump tweets attacks about the intelligence community, transparency groups and journalists often file FOIA requests (and subsequently lawsuits) seeking the documents that underpin his claims. The question that often comes up: Do Trump’s smartphone rants break the seal of secrecy on confidential programs?
The answer seems to be no. Multiple judges have sided with Justice Department lawyers, concluding that his Twitter disclosures do not mean that the government has to confirm or deny whether records about those activities exist.
In a FOIA case seeking documents that would show whether Trump is under investigation, U.S. District Judge Amy Berman Jackson said that the President’s tweets to that effect are “speculation.” Similarly, in a FOIA suit to get more information about the widely publicized dossier of potential ties between Trump and Russia, U.S. District Judge Amit Mehta said that the President’s statements are political rather than “assertions of pure fact.”
And so, whether Trump actually knows what he’s talking about remains an open question.
The Cross-Contamination Award - Stanford Law Professor Daniel Ho
One of the benefits of public records laws is they allow almost anyone—regardless of legal acumen—to force government agencies to be more transparent, usually without having to file a lawsuit.
But in Washington State, filing a public records request can put the requester at legal risk of being named in a lawsuit should someone else not want the records to be made public.
This is what happened to Sarah Schacht, a Seattle-based open government advocate and consultant. For years Schacht has used public records to advocate for better food safety rules in King County, an effort that led to the adoption of food safety placards found in restaurants in the region.
After Schacht filed another round of requests with the county health department, she received a legal threat in November 2018 from Stanford Law School professor Daniel Ho’s attorney threatening to sue her unless she abandoned her request. Apparently, Ho has been working with the health department to study the new food safety and placard regulations. He had written draft studies that he shared with the health department, making them public records.
Ho’s threat amounted to an effort to intimidate Schacht from receiving public records, probably because he had not formally published his studies first. Regardless of motive, the threat was an awful look. But even when faced with the threat, Schacht refused to abandon her request.
Fortunately, the lawsuit never materialized, and Schacht was able to receive the records. Although Ho’s threats made him look like a bully, the real bad actor in this scenario is Washington State’s public records law. The state’s top court has interpreted the law to require parties seeking to stop agencies from releasing records (sometimes called reverse-FOIA suits) to also sue the original requester along with the government agency.
The Scanner Darkly Award - St. Joseph County Superior Court
Courtesy of Jessica Huseman
ProPublica reporter Jessica Huseman has been digging deep into the child welfare system and what happens when child abuse results in death. While following up on a series of strangulations, she requested a copy of a case file from the St. Joseph County Superior Court in Indiana. Apparently, the clerk on the other end simply took the entire file and ran everything through a scanner. The problem was that the file contained a CD-ROM, and that’s not how CD-ROMs work. “Well this is the first time this had happened,” Huseman posted to Twitter, along with the blotchy black-and-white image of the top of the disc. “They scanned a CD as part of my FOI and didn’t give me its contents. Cool cool.”
The Cash for Crash Award - Michigan State Police
As tech companies experiment with autonomous vehicles on public roadways, reporters are keeping tabs on how often these cars are involved in collisions. That’s why The Information’s Matt Drange has been filing records requests for the crash data held by state agencies. Some government departments have started claiming that every line of the dataset is its own, individual record and subject to a copy fee. Our winner, the Michigan State Police, proposed to charge Drange a 25-cent fee for each of a 1.9 million-line dataset, plus $20 for a thumbdrive, for a grand total of $485,645.24, with half of it due up front. Runners-up that quoted similar line-by-line charges include the Indiana State Police ($346,000) and the North Carolina Department of Transportation ($82,000). Meanwhile, Florida’s government released its detailed dataset at no charge at all.
The Bartering with Extremists Award - California Highway Patrol
In 2016, the Traditionalist Worker Party (TWP), an infamous neo-Nazi group, staged a demonstration at the California State Capitol. Counter-protesters fiercely opposed the demonstration, and the scene soon descended into chaos, leaving multiple people injured. When the dust settled, a member of the public (disclosure: also a co-author of this piece) filed a California Public Records Act request to obtain a copy of the permit the white nationalist group filed for its rally. The California Highway Patrol rejected the request for this normally available document, claiming it was related to a criminal investigation.
Two years later, evidence emerged during criminal proceedings that a CHP detective used the public records request as a bargaining chip in a phone call with the TWP protest leader, who was initially reluctant to provide information. The officer told him how the request might reveal his name. “We don’t have a reason to...uh...deny [the request],” the officer said according a transcript of the call. But once the organizer decided to cooperate, the officer responded, “I’m gonna suggest that we hold that or redact your name or something...uh...until this thing gets resolved.” In light of these new facts, the First Amendment Coalition filed a new request for the same document. It too was denied.
The Preemptive Shredding Award - Inglewood Police Department
In defiance of the law enforcement lobby, California legislators passed a law (SB 1421) requiring police and sheriffs to disclose officer misconduct records in response to California Public Records Act requests. These documents, often contained in personnel files, had historically been untouchable by members of the public and the press.
Almost immediately, police unions across the Golden State began to launch lawsuits to undermine these new transparency measures. But the Inglewood Police Department takes the prize for its efforts to evade scrutiny. Mere weeks before the law took effect on Jan. 1, 2019, the agency began destroying records that were set to become publicly available.
“This premise that there was an intent to beat the clock is ridiculous,” Inglewood Mayor James T Butts Jr. told the LA Times in defending the purge. We imagine Butts would find it equally ridiculous to suggest that the fact he had also been a cop for more than 30 years, including serving in Inglewood and later as police chief of Santa Monica, may have factored into his support for the destruction of records.
The What the Swat? Award - Nova Scotia and Halifax Law Enforcement
One Wednesday morning in April, 15 Halifax police officers raided the home of a teenage boy and his family. “They read us our rights and told us not to talk," his mother would later tell CBC. “They rifled through everything. They turned over mattresses, they took drawers and emptied out drawers, they went through personal papers, pictures. It was totally devastating and traumatic."
You might well wonder, what was the Jack Bauer-class threat to geo-political stability? Nothing at all: The Canadian teen had just downloaded a host of public records from openly available URLs on a government website.
At the heart of the ordeal was some seriously terrible security practices by Nova Scotia officials. The website created to host the province’s public records was designed in such a way that every request and response had a nearly identical URL and placed no technical restrictions on the public’s ability to access any of the requests. This meant that regular public records requests and individuals’ requests to access government files about them, which included private information, were all stored together and available on the internet for anyone, including Google’s webcrawler, to access. All that was necessary was changing a number identifying the request at the end of the URL.
What Nova Scotian officials should have done upon learning about leaks in their own public records website’s problems was apologize to the public, thank the teen who found these gaping holes in their digital security practices, and implement proper restrictions to protect people’s private information. They didn’t do any of that, and instead sought to improperly bring the force of Canada’s criminal hacking law down on the very person who brought the problem to light.
The whole episode—which thankfully ended with the government dropping the charges—was a chilling example of how officials will often overreact and blame innocent third parties when trying to cover up for their own failings. This horror show just happened to involve public records. Do better, Canada.
The Outrageous Fee Request of the Year - City of Seattle
When self-described transparency advocate and civic hacker Matt Chapman sent his request to Seattle seeking the email metadata from all city email addresses (from/to/BCC addresses, time, date, etc), he expected some pushback, because it does sound like an incredible amount of data to wrangle.
Seattle’s response: All the data can be yours for a measly $33 million. Officials estimated that it would take 320 years worth of staff time to review the roughly 32 million emails responsive to Chapman’s request. Oh, and they estimated charging an additional $21,600 for storage costs associated with the records. The fee request is the second highest in the history of The Foilies (the Department of Defense won in 2016 for estimating it would take $660 million to produce records on a particular computer forensic tool).
Then the city did something entirely unexpected: It revisited the fee estimate and determined that the first batch of records would cost only $1.25 to process. We get it, math is hard.
But wait—that’s not all. After paying for the batches of records with a series of $1.25 checks, Chapman received more than he ever bargained for. Rather than disclosing just the metadata for all 32 million emails, Seattle had given him the first 256 characters of every email. Those snippets included passwords, credit card numbers, and other personally identifying information.
What followed was a series of conversations between Chapman, Seattle’s lawyers, and the city’s IT folks to ensure he’d deleted the records and that the city hadn’t just breached its own data via a public records request.
Ultimately, Seattle officials in January 2018 began sending the data to Chapman once more, this time without the actual content of email messages. The whole episode doesn’t exactly inspire confidence in Seattle officials’ ability to do basic math, comply with the public records law or protect sensitive information.
The Intern Art Project Award - Vermont Gov. Phil Scott
Seattle isn’t the only city to stumble in response to Matt Chapman’s public records requests for email metadata. The Vermont governor’s office also wins for its scissor-and-glue approach to releasing electronic information.
Rather than export the email information as a spreadsheet, the Vermont governor’s office told Chapman it had five interns (three of whom were unpaid) working six hours each, literally “cutting and pasting the emails from paper copies.” Next thing Chapman knew, he had a 43-page hodgepodge collage of email headers correlating with one day’s worth of messages. The governor’s attorney told Chapman it would cost $1,200 to process three more days’ worth of emails.
Chapman pushed back and provided his own instructions on exporting the data using a computer and not, you know, scissors and glue. Sure enough, he received a 5,500-line spreadsheet a couple weeks later at no charge.
The Least Transparent Employer Award - U.S. Department of Justice
In the last few years, we’ve seen some great resignation letters from public servants, ranging from Defense Secretary James Mattis telling President Trump “It’s not me, it’s you” to former Attorney General Jeff Sessions’ forced resignation.
But the Trump DOJ seems to have had enough of the tradition and has now determined that U.S. Attorney resignation letters are private in their entirety and cannot be released under the Freedom of Information Act. Of course, civil servants should have their private information protected by their employer, but that’s precisely what redactions should be used to protect.
Past administrations have released resignation letters that are critical of executive branch leaders. The change in policy raises the question: What are departing U.S. Attorneys now saying that the government wants to hide?
The Clawback Award - The Broward County School Board
After the tragic Parkland shooting, the South Florida Sun-Sentinel went to court to force the Broward County School Board to hand over documents detailing the shooter’s education and disciplinary record. A judge agreed and ordered the release, as long as sensitive information was redacted.
But when reporters copied and pasted the file into another document, they found that the content under the redactions was still there and readable. They broke the story of how the school denied the shooter therapeutic services and alternative education accommodations, but then uploaded the school board’s report with working redactions.
Rather than simply do better with double-checking their redactions next time, the school board struck back at the newspaper. They petitioned the court to hold the newspaper in contempt and to prevent anyone from reporting on the legally obtained information. Although the local judge didn’t issue a fine, she lambasted the paper and threatened to dictate exactly what the paper could report about the case in the future (which is itself an unconstitutional prior restraint).
The Wrong Way to Plug a Leak Award - City of Greenfield, California
The Monterey County Weekly unexpectedly found itself in court after the city of Greenfield, California sued to keep the newspaper from publishing documents about the surprising termination of its city manager.
When Editor Sara Rubin asked the interim city manager for the complaint the outgoing city manager filed after his termination, she got nothing but crickets. But then, an envelope containing details of a potential city political scandal appeared on the doorstep of one of the paper’s columnists.
The weekly reached out to the city for comment and began preparing for its normal Wednesday print deadline. Then, the morning of publication, the paper got a call saying that they were due in court. The city sued to block publication of the documents, to have the documents returned and to have the paper reveal the identity of the leaker.
Attorney Kelly Aviles gave everyone a fast lesson in the First Amendment, pointing out that the paper had every right to publish. The judge ruled in the paper’s favor, and the city ended up paying all of the Monterey County Weekly’s attorney fees.
If it Looks like a Duck Award - Brigham Young University Police

Brigham Young University’s Police Department is certified by the state,* has the powers of the state, but says that they’re not actually a part of government for purposes of the Utah transparency law.
After the Salt Lake Tribune exposed that the University punished survivors of sexual assault for coming forward and reporting, the paper tried to get records of communications between the police department and the school’s federally required sexual assault coordinator. BYU pushed back, saying that the police department is not subject to Utah’s Government Records Access and Management Act because the police department is privately funded.
This actually turns out to be a trickier legal question than you’d expect. Brigham Young University itself isn’t covered by the state law because it is a private school. But the university police force was created by an act of the Utah legislature, and the law covers entities “established by the government to carry out the public’s business.” Investigating crime and arresting people seems like the public’s business.
Last summer, a judge ruled that the police department is clearly a state agency, but the issue is now on appeal at the Utah Supreme Court. Sometime this year we should learn if the police are a part of the government or not.
*Because BYU police failed to comply with state law, and was not responsive to an internal investigation, the Utah Office of Public Safety notified the department on February 20th that the BYU police department will be stripped of its certification on September 1, 2019. The University police also plan to appeal this decision.
The Insecure Security Check Award - U.S. Postal Service
Congressional elections can turn ugly, but the opponent of newly elected U.S. Rep. Abigail Spanberger got a boost when the U.S. Postal Service released Spanberger’s entire personnel file, including her security clearance application, without redaction of highly sensitive personal information.
When a third party requests a person’s federal employment file without the employee’s permission, the government agency normally releases only a bare-bones record of employment dates, according to a Postal Service spokesperson. But somehow Rep. Spanberger wasn’t afforded these protections, and the Postal Service has potentially made this mistake in a “small number” of other cases this year. Security clearance applications (Form SF-86) are supposed to be analyzed and investigated by the FBI, raising questions about how the FOIA officer got the information in the first place. The Postal Service has apologized for the mistake, which they say is human error, but maybe security clearance applications should be kept just as secure as the state secrets the clearance is meant to protect.
The Foilies were compiled by Electronic Frontier Foundation Senior Investigative Researcher Dave Maass, Staff Attorney Aaron Mackey, Frank Stanton Fellow Camille Fischer, and Activist Hayley Tsukayama. Illustrations by EFF Art Director Hugh D'Andrade. For more on our work visit eff.org.