For the hundreds of thousands of users searching for that special someone through one of the largest free online dating sites, the love fest may be coming to an end. OkCupid is putting users’ privacy in danger by failing to support secure access to its entire website through HTTPS. Every OkCupid email, chat session, search, clicked link, page viewed, and username is transmitted over the Internet in unencrypted plaintext, where it can be intercepted and read by anyone on the network.

Screen shot from OkCupid Help Forum. While passwords after inital signup aren’t sent in the clear, there are other severe security problems with OkCupid.com.
“HTTPS” is standard web encryption that ensures information sent and received online is encrypted instead of as plaintext. OkCupid does not enable HTTPS across the site, which means that while OkCupid doesn’t leak passwords entered during log in over plaintext, it does leak a lot of other sensitive data. OkCupid’s failure to offer HTTPS support potentially exposes:
- Email content from within OkCupid
- Content of online chats on OkCupid
- Searches conducted on the site
- Every unique page viewed, and thus all profiles looked at
- Content of “hidden” questions–questions a user responds to in order to improve match results but then marks as “private” so others cannot see his or her response
Failing to offer HTTPS is particularly unfortunate because OkCupid offers a variety of privacy-enhancing ways of limiting who can access your profile. For example, users who mark their sexual orientation as gay or bisexual may opt not to allow their profile to be seen by straight individuals. This feature might be useful for someone who is looking to date a same-sex partner but is not openly queer among others in their community. Unfortunately, your profile data, including the fact that you identify as gay and don’t wish to be seen by straight people, is transmitted over plaintext.
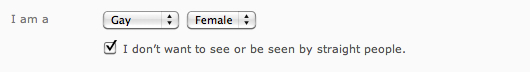
OkCupid provides privacy controls to limit who sees your profile, including limiting whether heterosexual users can see your profile.
Other privacy-enhancing features such as limiting who can view your profile (to everyone, members of OkCupid, your favorites, or no one at all) can be circumvented easily by someone monitoring your plaintext communication with OkCupid.
It’s even worse than you imagined.
The failure to encrypt your communications exposes sensitive data in online profiles to eavesdroppers, who could snoop on the content of your profile to learn about sensitive topics like religious and political beliefs, drug use, and sexual practices. The failure to encrypt also exposes the HTTP cookie that’s used to authenticate you to the site, which means that the eavesdropper can actually take over your account and impersonate you, even without knowing your password.

OkCupid lets users answer questions to help them improve their matches. Users are given privacy controls to answer questions "privately"—though the data is still transmitted in plaintext.
Although security experts have warned about this problem for over a decade, this attack was sometimes dismissed as theoretical or difficult to pull off. But all that changed with the release of Firesheep, a simple tool that can be used on shared wifi networks to take over web-based accounts on non-HTTPS sites. This type of eavesdropping is trivial for someone with even basic skills.
Firesheep lets an attacker take over an account by stealing a cookie without actually knowing the account password. For example, when you sit in a coffee shop using a shared network and log into a site that does not have HTTPS enabled, someone using the same networking could monitor what you are doing and even impersonate you.
Because OkCupid’s login form is also delivered over insecure HTTP, a more sophisticated attacker could also tamper with the login form itself, replacing it with a version that disables HTTPS entirely in order to learn the user’s password.
Major sites like Facebook and Twitter have come to appreciate these threats and offered meaningful, comprehensive HTTPS support to protect their users. These actions are in alignment with former Federal Trade Commissioner Pamela Jones Harbour’s call for websites to adopt HTTPS. Unfortunately, dating sites like OKCupid are lagging behind—way behind.
Tell OkCupid to protect your privacy
Many avid fans of OkCupid want to let the service know that they shouldn’t cut corners when it comes to security. Send OkCupid a message here.
Individual emails from users can be effective in prompting a website to improve their security practices, as shown by @MayMaym's successful campaign to get HTTPS support on Fetlife.com.