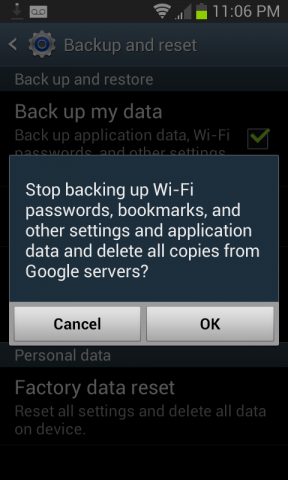
If you have a recent Android phone or tablet, chances are you take advantage of a convenient feature to backup your application settings and wireless network passwords. This feature is enabled by default in Android 2.2 and later, and it can make switching to a new device or replacing a lost phone a quicker process. If you haven't examined all the settings for your phone, you might not know if this setting is enabled.
You might not even know who has access to your data.
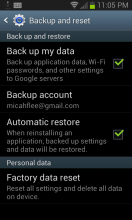
When a Google user sets up a new Android device with Google Play and signs into her Google account, Android Backup Service automatically downloads any backed up settings and wireless network passwords from Google's servers. All that is required of the user to begin this process is her Google credentials.
This indicates that the data is stored either in plaintext, or encrypted using Google account credentials only. In the latter case, it would need to be decrypted before transit to the user's device. However, a statement from Google to Ars Technica indicates that the former might be the case:
"Our optional 'Backup my data' feature makes it easier to switch to a new Android device by using your Google Account and password to restore some of your previous settings. This helps you avoid the hassle of setting up a new device from scratch. At any point, you can disable this feature, which will cause data to be erased. This data is encrypted in transit, accessible only when the user has an authenticated connection to Google and stored at Google data centers, which have strong protections against digital and physical attacks."
This statement makes clear that the data is encrypted in transit, which is good. But it doesn't say that the data is encrypted at rest. If it's not, authorized Google employees could access it or make it available to government data requests. We hope that Google is storing this data in an encrypted form such that only the user can unlock it.
How sensitive is this data? Settings data is generally limited to the options you select when configuring your device. It may also include a list of software you have downloaded from the Google Play Store.
Your wireless network passwords might be considered very sensitive. While you personally might not be too worried about sharing the encryption key for your home network, your employer might feel differently. In either case, since the network administrator has made the decision to secure the network, any developer designing software to store the network password should respect that decision and assume that the password wasn't meant to be left lying around in plain sight or plaintext.
Fixing the flaw is more complicated than it might seem. Android is an open source operating system developed by Google. Android Backup Service is a proprietary service offered by Google, which runs on Android. Anyone can write new code for Android, but only Google can change the Android Backup Service.
Google already has a great model for this kind of service in Chrome. Chrome's sync service allows a user to store all her settings on Google's servers, encrypted. By default, the data is encrypted with her Google credentials, but Chrome offers the additional option to encrypt this data with the user's own sync passphrase. This model would work very well for Android Backup Service.
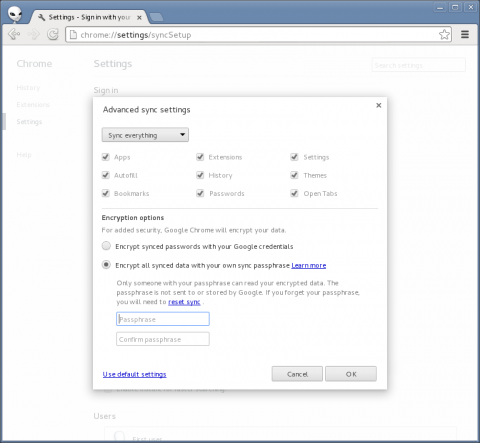
Additionally, the open source Android OS itself could offer client side encryption as part of the backup code that Android Backup Service is built on. That way, third-party providers could more easily safeguard your data.
Cloud storage of personal data has become a ubiquitous part of the computing landscape, and of our daily lives. With frequent revelations of government, corporate, and entirely unauthorized abuse of that personal data, it's important to examine what we give to cloud providers, when, and how. The standard we'd like to see providers move toward is host-proof hosting, especially when backing up sensitive data. It might be reasonable to trust these companies at times in order to take advantage of the convenience their services offer, but trusting a service that mishandles one's data by failing to properly secure it is clearly a mistake.
Google says, "You should only give your WiFi password to people you trust." If Google has mapped our wireless networks and stored their passwords, they need to act fast to restore that trust.