Last week, when the Assad regime shut down the Internet across the country for three days, one of the few IP addresses to stay online was the address implicated in the ongoing campaign of surveillance malware targeting Syrian dissidents since November 2011, including a fake anti-hacking tool, a fake Skype encryption tool, and fake documents allegedly pertaining to the formation of the leadership council of the Syrian revolution. Now EFF has detected two new campaigns of surveillance malware associated with the same IP address--the first we have detected since this summer.
The first campaign began on November 21st, coinciding with a week in which the Syrian opposition made considerable headway against the Assad regime. Users are enticed to download a file called "اسماء بعض الممولين في سوريا والخارج المطلوبين لدى النظام السوري_m-fdp.scr," (hash: ed86876db98db35d8c205f8c0b92b0a4) which translates roughly as "Names of some financiers in Syria and abroad who are wanted by the Syrian regime _m-fdp.scr." This file appears to be a PDF, but is actually a self-extracting rar archive in the form of an executable .scr (screensaver file). Immediately after the Internet shutdown ended on December 1st, a new version of this campaign was distributed, this time enticing users to download a document called "اسماء بعض المسلحين في سورية والخارج المطلوبين لدى النظام السوري2012_m-fdp.scr," (hash: 02c2ee77cf5aaf8ac03739640c46e822) roughly translated as "Names of some militants in Syria and abroad who are wanted by the Syrian regime 2012_m-fdp.scr."
Users were contacted via Skype and social media platforms, possibly through accounts that had been compromised, and encouraged to download these files from two Mediafire links, shown in the screenshots below: http://www.mediafire.com/?btdkh64ebedrc0h Rather than sending short, spammy messages, these conversations are reported to be highly interactive.

http://www.mediafire.com/?zr42ka5838ev4po

Syrian Internet users should be extremely cautious about clicking on suspicious-looking links, or downloading documents over Skype, even if the document purportedly comes from a friend.
Both of these links have been disabled by Mediafire for abuse.
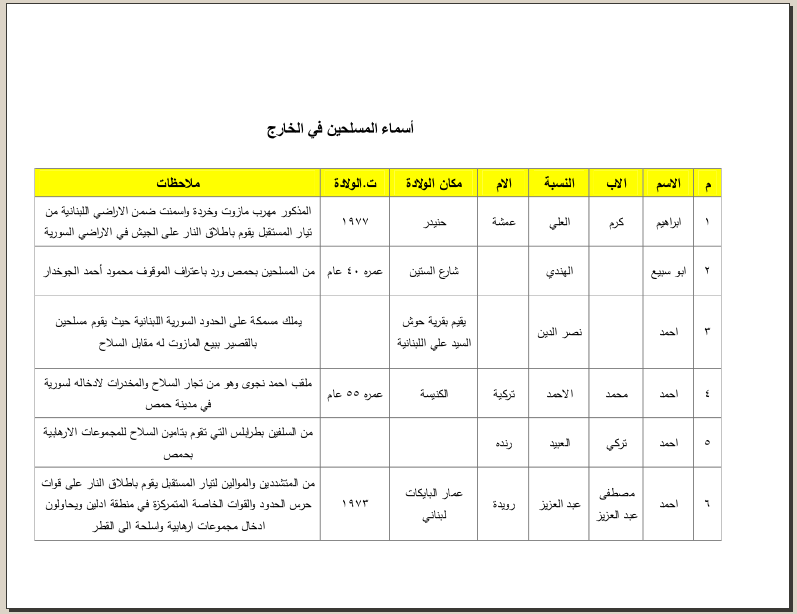
On execution, this link opens a 285-page file which allegedly contains names and personal information about people who are wanted by the Assad regime for their involvement in the opposition movement. The file is shown in the screenshot below.

Opening the file displays a PDF, shown in the screenshot below. It also installs a remote administration tool called DarkComet RAT, which can capture webcam activity, disable the notification setting for certain antivirus programs, record key strokes, steal passwords, and more. Over a dozen of the attacks EFF has analyzed have installed versions DarkComet RAT. It's increasingly close association with pro-Syrian-government hackers, combined with the Human Rights Watch report on the Assad regime's network of torture centers, may have motivated the project's sole developer to shut it down, declaring his intention to work on an alternative tool that more closely resembles VNC and requires administrative access to install. While DarkComet RAT is no longer supported by its original developer, it is still the covert surveillance tool of choice for this persistent group of pro-Syrian-government actors.
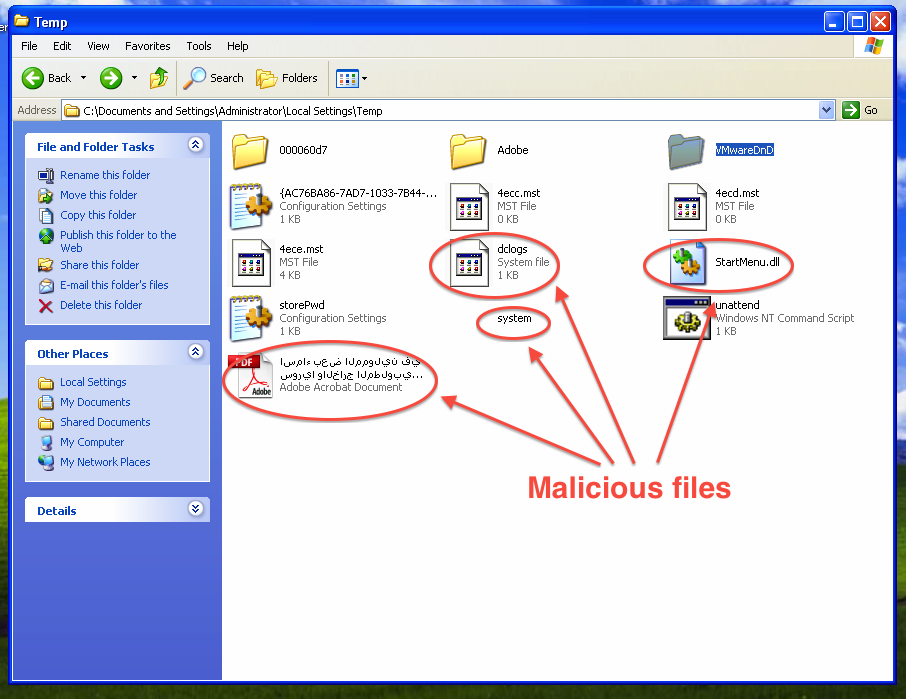
DarkComet RAT drops the following files, shown in the screenshot below:
C:\DOCUME~1\ADMINI~1\LOCALS~1\Temp\system.exe
C:\DOCUME~1\ADMINI~1\LOCALS~1\Temp\StartMenu.dll
C:\DOCUME~1\ADMINI~1\LOCALS~1\Temp\اسماء بعض الممولين في سوريا والخارج المطلوبين لدى النظام السوري.pdf
Additionally, once you start typing, it creates a keylogger file called C:\DOCUME~1\ADMINI~1\LOCALS~1\Temp\dclogs.sys, which is also shown.
It also creates C:\Documents and Settings\Administrator\Start Menu\Programs\Startup\..lnk, shown in the screenshot below:

It communicates with the remote command and control server at 216.6.0.28 on port 885
TCP 0.0.0.0:0 Connect 216.6.0.28:885
This IP address is owned by the STE (Syrian Telecommunications Establishment) and is registered in Damascus.
These two Trojans are detected by some anti-virus software at this time, but the sale of AV software from the United States to Syria is currently banned under U.S. export controls--just one more example of the ways in which export controls keep Syrians accessing the tools they need to protect themselves from government surveillance.
DarkComet RAT is also detected by the DarkComet RAT Removal Tool, written by the same developer that originally wrote DarkComet RAT. The screenshot below shows the removal tool detecting DarkComet RAT on an infected computer.

If your computer is infected, removing DarkComet RAT does not guarantee that your computer will be safe or secure. This attack eventually gives an attacker the ability to execute arbitrary code on the infected computer. There is no guarantee that the attacker has not installed additional malicious software while in control of the machine. The safest course of action is to re-install the operating system on your computer and change all passwords to accounts you may have logged into while the computer was infected.
EFF is deeply concerned by the reemergence pro-government malware targeting online activists in Syria. We will continue to keep a close eye on developments in this area.









