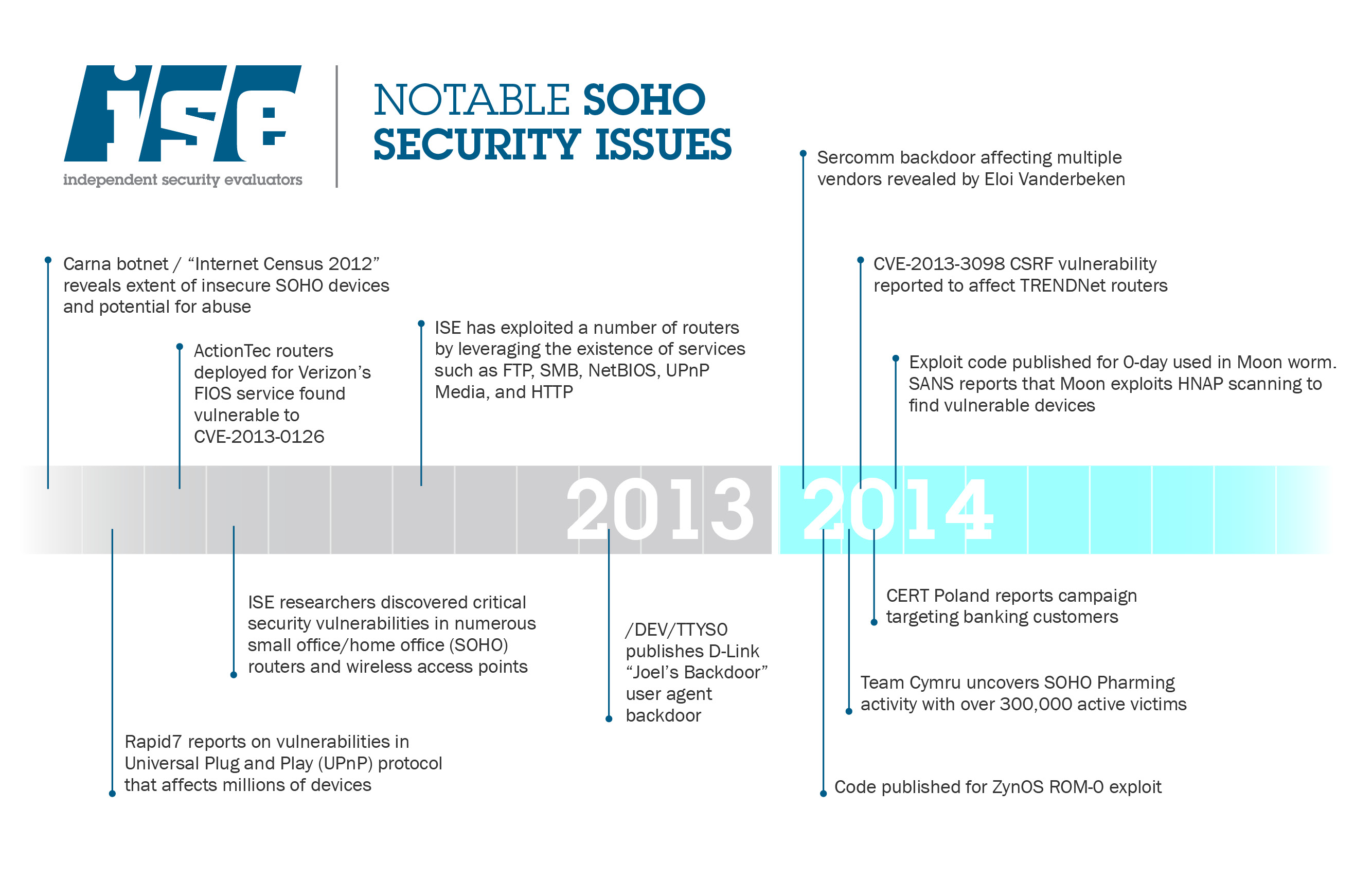
As part of our Open Wireless Movement, we set out to create router software that would make it easier for people to safely and smartly share part of their wireless network. Protecting hosts, so their security is not compromised because they offer open networks, is one of the goals of the router software we released. However, as research published by Independent Security Evaluators (ISE) and others has shown, almost every popular home router has serious security flaws.
In developing the router software, we realized that we also needed to tackle the more fundamental problem of home router security. Instead of just creating an open-wireless friendly router, why not work to improve router security while we're at it?
With this in mind, we're teaming up with ISE to host "SOHOpelessly Broken," a router hacking contest this year at DEF CON 22. Focusing on small office/home office (SOHO) equipment, this contest will reward the discovery of zero-day vulnerabilities in fully updated, popular off-the-shelf SOHO routers, as well as pit contestants against each other in a capture-the-flag style competition targeting routers with outdated, known-vulnerable firmware. (Naturally, all vulnerabilities discovered as part of the contest must be responsibly disclosed to the manufacturer.)
You can sign up to participate on the SOHOpelessly Broken website.
By joining, you'll also have a chance to hack away at our Open Wireless Router. It's looking more and more like our project will be the first home router and firmware—that we know of—to undergo regular, public, third-party security assessments. We also plan to be one of a few router firmwares to automatically self-update with new security patches, eliminating what has been a cumbersome and often-ignored process for consumers—largely at no fault of their own.
Your Router is Probably Insecure, which Can Cause Serious Harm
Last year, researchers at ISE found that a staggering 100% of SOHO routers they evaluated were vulnerable to remote attacks. And a recent study found that 80% of Amazon's top 25 best-selling SOHO wireless routers had security issues. Vulnerabilities revealed in these devices ranged from blatantly obvious issues to absurdly inappropriate back doors. The "moon worm" and several other notable exploits of SOHO routers demonstrate that these issues are not only interesting on a theoretical level, but are appearing in the wild and directly affecting consumers. In some cases, the vulnerabilities exploited were the very same that were discovered and reported months earlier—while the router manufacturer had issued a patch, the issues remained in some router models.
Compromising a router gives an attacker several options for exploitation. Most common are attacks on the domain name system (DNS) used to look up IP addresses. Attackers can point a DNS query to servers that are under their control, thereby redirecting the user to a malicious server, such as a fake banking webpage. The attacker can then steal valuable personal information and passwords. For example, a large-scale operation to steal banking credentials in this manner was identified in Poland this year.
Another use of compromised routers (e.g., through malware that functions like the "moon worm") is to make them part of the botnets that launch spam, phishing, account hijacking, identity theft, and distributed denial-of-service (DDoS) attacks. If we can make it harder for botnets, we can help improve security around the world.
Finally, with the continuing increase of internet connected equipment in homes, a compromised home router affords an attacker a strategic vantage point to launch attacks on targets such as home medical, home automation, or home security equipment.
We Can Build A Better Router
With our Open Wireless Router project and ISE's SOHOpelessly Broken hacking contest, we hope to further demonstrate how insecure these devices are, as well as show the consequences of leaving these security issues unmitigated by the manufacturer or unpatched by the consumer.
Without immediate and dramatic industry-wide improvement, vulnerable routers will remain a threat to individuals, small business, and large enterprises alike. These woefully insecure devices expose our persons and our companies, not just to an invasion of privacy, but to fraud, theft, loss of sensitive data, outages, and disruption of business. It has been over a year since ISE's important research was published, yet not enough has been done. We hope that by raising awareness through our contest and by providing an alternative through our Open Wireless Router, we will move the state of the art in wireless networking in the right direction.