The world learned in 2011 that a U.S. company's Internet censorship and surveillance technology is in the hands of the Syrian government. This was notable because Syria is under heavy sanctions by the U.S. government—meaning there’s no way that it was legal for Syria to end up with this American-made hardware and software. While the tech firm, Blue Coat Systems, initially denied knowledge of the sale (which was uncovered by activists at Telecomix and elsewhere), the U.S. Department of Commerce nonetheless launched an investigation into how their equipment found its way into the country.
The recently released investigation confirms our previous recommendation that companies selling surveillance and censorship technologies absolutely must take steps to know their customer and that this must mean identifying the actual ultimate purchaser of a product even when there is a middleman, or multiple middlemen. Without it, their products can and will fall into the hands of authoritarian regimes.
Last month, the U.S. Department of Commerce revealed that Computerlinks FZCO, the Middle East/North African division of the multinational Computerlinks AG, was the middleman between Blue Coat and the Syrian government. The resulting order, published on April 25, 2013 by the Bureau of Industry and Security (BIS) details how Computerlinks violated export laws three times, ultimately selling tools worth $1.4 million to Syria to spy on its people. Computerlinks settled with BIS for a $2.8-million fine.
We also now know that 18 separate IT companies (including big names such as EMC, Symantec and McAfee) are continuing to contract with Computerlinks FZCO, even though the company was just penalized for breaking the Syrian trade embargo.
Some Background
In 2011, the hacktivist group Telecomix released evidence that Internet surveillance and censorship products developed by Silicon Valley-based Blue Coat were in use in Syria. At first Blue Coat pleaded ignorance, but later confirmed to the Wall Street Journal that at least 13 of the ProxySG appliances destined for other nations ended up in Syria.
Blue Coat conducts overseas dealings through third-party distributors or "channel partners." As the channel partner in this case, the Dubai branch of Computerlinks told Blue Coat the technology was being sold to the Iraq Ministry of Telecom and LiwalNet, an ISP in Afghanistan.
While it is legal to sell certain technologies to Iraq and Afghanistan, neither of these countries is a model of openness and transparency. For example, a bill proposed in Iraq last year would have imposed mandatory life sentences for certain computer “crimes.”
But Computerlinks didn’t sell to Iraq or Afghanistan; rather, it used yet another middleman to sell Blue Coat’s technology to the state-run Syrian Telecommunications Establishment—not once, but on three separate occasions. In at least one documented instance, Computerlinks knew it was providing tech support that was designed to help Syria monitor the Web activities of individual users and prevent users from circumventing censorship controls.
In December 2011, the BIS added the go-between, Waseem Jawad of Infotec/Info Tech, to the BIS Entity List, which means he can no longer sell American goods. Computerlinks FZCO now must pay the statutory maximum fine, plus submit to mandatory independent audits.
"Today’s settlement reflects the serious consequences that result when companies evade U.S. export controls," Under Secretary for Industry and Security Eric L. Hirschhorn said in a press statement. "It is the result of an aggressive investigation and prosecution by BIS of the unlawful diversion of U.S. technology to Syria. It is vital that we keep technology that can repress the Syrian people out of the hands of the Syrian government."
What about Blue Coat?
While it now seems clear that Computerlinks directly provided the hardware, software, and support to Syria, questions remain about Blue Coat’s role.
In its own press release, Blue Coat commended BIS and portrayed the settlement as a vindication, maintaining its position that it was lied to by Computerlinks FZCO.
More importantly, however, Blue Coat at least sounds like it understands that it has to do more, and hopefully even grasps the need to go beyond the narrow question of countries under U.S. sanctions or other export rules to ensure that its products aren’t used to facilitate human-rights abuses.
In a February 15, 2013 blog post titled, “Enabling a Safe and Productive Internet,” Blue Coat’s chief operating officer and president David Murphy addressed the issue of human rights:
"We believe our products play a vital role in protecting the global connectivity that the Internet provides, and we take seriously recent press and other reports that have implied our products are being misused for malign [sic] purposes. Blue Coat respects and supports freedom of expression, which the U.N. has declared to be a universal human right for all people. We do not design our products or condone their use to suppress human rights."
He continued: “Throughout 2013 we will continue to engage key stakeholders, including our channel partners, to review what further steps we can take to limit misuse of our products. “ The company also told investors it severed ties with Computerlinks FZCO.
That’s good to hear. But while promises of "stakeholder engagement" are nice, more is plainly need. According to a January 15, 2013 report by Citizen Lab researchers, Blue Coat technology continues to turn up in problematic countries such as China, Burma, India, Thailand, Turkey, Venezuela and Nigeria. Reporters Without Borders gave Blue Coat a prominent entry on its list of “Corporate Enemies of the Internet.”
As EFF’s Jillian York wrote:
"Blue Coat's blatant lack of concern for human rights is alarming. There are far more repressive regimes in the world than there are embargoed countries. Several United States allies, including Bahrain, Saudi Arabia, and Qatar, are also using Blue Coat systems for censorship and surveillance. But Blue Coat is surely unconcerned; after all, exporting to those countries isn't against the law; it just helps violate the human rights of the people living under those regimes."
So let’s start with the engagement, Blue Coat. EFF is very happy to assist, and for starters, we suggest Blue Coat's leadership consider our Know Your Customer proposal, which includes a two-pronged framework for surveillance technology companies like Blue Coat that wish to adopt voluntary standards to protect human rights when dealing with foreign governments. First, firms should affirmatively investigate potential clients, the end users and third-party brokers, both before and during the sale. Second, firms should refrain from doing business with governments when “know your customer” investigations turn up credible evidence of human rights abuses involving their clients, brokers or end users.
While it’s difficult to know for sure, it seems more likely that Blue Coat would have found out what Computerlinks FZCO was up to if it had followed these standards, especially since there were multiple sales over time that were wrongly diverted.
Although more of the story has now come to light, questions remain, especially in light of a Telecomix report on May 23 that claims 34—not 13—Blue Coat servers are operating in Syria. If true, we want to know how those additional servers got there.
Surveillance Tool Makers: You are being Watched
Computerlinks FZCO agreed to the settlement, and also agreed not to deny the charges, but also did not admit guilt.
"The company is happy to have the matter resolved ... and is moving forward with its business,” a spokesperson for Computerlinks AG, the parent company of Computerlinks FZCO, told CNBC.
And moving on it is: According to Computerlinks’ United Arab Emirates website, 18 companies still use the firm to distribute IT products in the Middle East, despite the Blue Coat judgement. These include Crossbeam, EMC, Exinda, Extreme Networks, F5, Gigamon, Infoblox, Juniper Networks, McAfee, NCP, PGP, Q1 Labs, RSA, Skybox Security, Sophos, Symantec, Trend Micro, and Websense. More than 80 companies are listed on Computerlinks’ overall worldwide directory of vendors.
The $2.8 million fine would not seem much of a deterrent to Computerlinks’ bottom line: In 2012, the company saw its annual revenue jump 22 percent to $1.25 billion. Nor will the audit requirement ensure accountability: It only applies to the Dubai subsidiary, not the company as a whole, which is attempting to brand itself as “The Next Generation Distributor.”
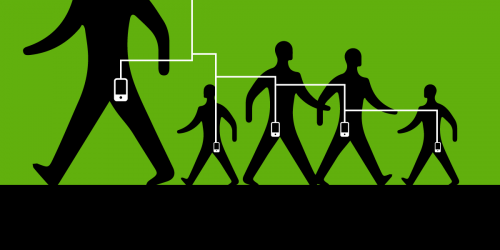
Tech companies working with ComputerLinks, you are now on notice: If you develop products that could be used to surveil or censor, you should reconsider whether this company deserves your trust. At a minimum, you should take steps to ensure they're telling the truth about where they're sending your products.
These three words are worth repeating: Know. Your. Customer. If you don't put controls in place, you could end up supplying despots around the world with the technology to commit human-rights violations.
Perhaps you might also reconsider altogether the long-term ramifications of designing and marketing the spy tools that seem to be so popular with repressive dictatorships.
One last note to Blue Coat: You're not off the hook yet.1
- 1. At the end of 2012, Blue Coat acquired Crossbeam, which still distributes its products through Computerlinks FZCO.