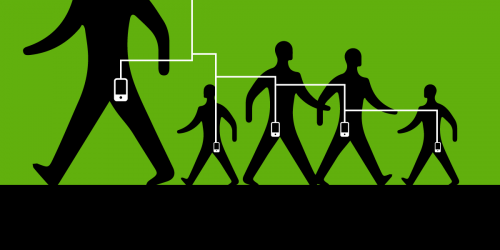
Cisco custom-built the so-called “Great Firewall of China,” also known as the “Golden Shield.” This system enables the Chinese government to conduct Internet surveillance and censorship against its citizens. As if that weren’t bad enough, company documents also revealed that, as part of its marketing pitch to China and in an effort to meet its customers needs, Cisco built a special Falun Gong module into the Golden Shield that helped the Chinese authorities identify, locate, and ultimately persecute practitioners of that religion by, for example, creating profiles of them that could be used during interrogations and forced conversions (i.e., torture).
Five years ago, victims sued Cisco for the human rights abuses they suffered as a result of the Falun Gong module. The case, Doe I v. Cisco Systems, is currently pending before the U.S. Court of Appeals for the Ninth Circuit. The plaintiffs are Falun Gong practitioners who allege that the company knowingly and purposefully designed and sold specific technologies to the Chinese government that aided and abetted human rights abuses, including torture, against them. We filed an amicus brief in January in favor of the plaintiffs.
Cisco recently submitted its responsive appellate brief (and the plaintiffs filed their reply) and one of its arguments made us do a double-take. Cisco claims that because U.S. export law doesn't ban it from selling its equipment to China, the company is immune from civil liability for the human rights abuses it facilitated. Cisco even went so far as to argue that the U.S. government’s recent dropping of overbroad proposed rules for regulating surveillance technologies under the Wassenaar Arrangement—rules that EFF strongly argued should be dropped—establishes that Cisco should be immune.
Specifically, Cisco argues that since Congress and the Department of Commerce regulate exports to China of guns and other “crime control and detection” equipment but do not ban the export of the “Internet infrastructure” products that Cisco sells, Cisco should be held completely immune for aiding and abetting human rights abuses.
There are two insurmountable problems with this argument.
First, the suggestion that the lack of a prohibition on export creates an immunity from civil liability is wrong.
Cisco tries to use the “political question doctrine,” a rule crafted by the Supreme Court to bar courts from reviewing policy choices and making decisions on policy matters, particularly those related to foreign relations, that should be left to Congress or the executive branch. However, the Supreme Court has made clear that courts have authority to hear matters that are “legal in nature.” Thus “it goes without saying that interpreting congressional legislation is a recurring and accepted task for the federal courts,” the Court said. This is true even if a court’s “decision may have significant political overtones."
Not only did Congress not expressly immunize Cisco from legal liability for selling its products to the Chinese government, a well-settled law applies that allows the company to be sued: the Alien Tort Statute (ATS). The ATS allows non-citizens to file lawsuits in U.S. courts for wrong-doing, such as human rights abuses, that violate international law. Thus, this case is about a violation of the ATS (and other laws), not about policy choices. Many cases have political overtones, including international overtones. But that doesn’t mean any case involving exports is so “political” as to be barred from judicial review. The courts have a duty to interpret the ATS to determine whether Cisco can be held liable for breaking U.S. law by knowingly and purposefully assisting in human rights abuses suffered abroad.
Second, the fact that Congress hasn’t banned the export of general “Internet infrastructure” technology to China doesn’t address whether Cisco, in selling its specific and customized “Internet infrastructure” (i.e., surveillance) technology to the Chinese government—understanding that it was going to be used in the persecution of Falun Gong practitioners—violated the ATS.
Finally, Cisco wrongly claims that it can’t be sued for facilitating human rights abuses because the Commerce Department tried, and then backed off of, adding “surveillance technologies” to the Wassenaar Arrangement, a 2013 international agreement that the U.S. signed to control the export of “dual-use” technologies (i.e., those that governments can use for both legitimate purposes and to violate human rights). The Commerce Department withdrew its 2015 proposed rules to implement the agreement after much public opposition, led in part by EFF.
We opposed the proposal because it was overbroad and would have had serious unintended consequences for the good guys—the information security researchers, penetration testers, security consultants, academics, and other hackers who try to improve security and privacy online. In other words, the regulations, in attempting to control surveillance software, would have made it difficult to create and share security software that we all rely on. We were pleased that the Commerce and State Departments recently agreed to renegotiate the Wassenaar Arrangement’s language at the multinational level.
But none of this has anything to do with whether companies like Cisco can be sued for customizing and selling surveillance technologies to repressive regimes with the understanding that they will be used to violate human rights. Cisco’s attempt to try to leverage the Wassenaar discussions into legal immunity for itself is unfounded and should fail.
Ultimately, we believe that export regulations are not the most effective mechanism for protecting human rights, a point underscored by the fact that notorious spyware seller Hacking Team regularly received export clearance by its home country Italy under the Wassenaar Arrangement. Rather, it is critically important that actual victims of human rights abuses—such as the plaintiffs in the ATS case against Cisco—have direct legal mechanisms to seek justice.