Update 2015-05-12: The Let's Encrypt client has now been renamed to Certbot. And Let's Encrypt has now issued over three million certificates!
Yesterday, the Let's Encrypt CA issued its millionth certificate. This is a perfect occasion for us to talk about some plans for the CA and client software through the rest of 2016.
In April of this year, all of the clients for Let's Encrypt will be renamed to be clearly distinct from the CA service offered by ISRG. The Let's Encrypt python client has primarily been an EFF project, so we'll start hosting it to make that clear.1
The python client is currently the most popular — though by no means the only — way to get certs from Let's Encrypt. We expect it will continue to be popular:
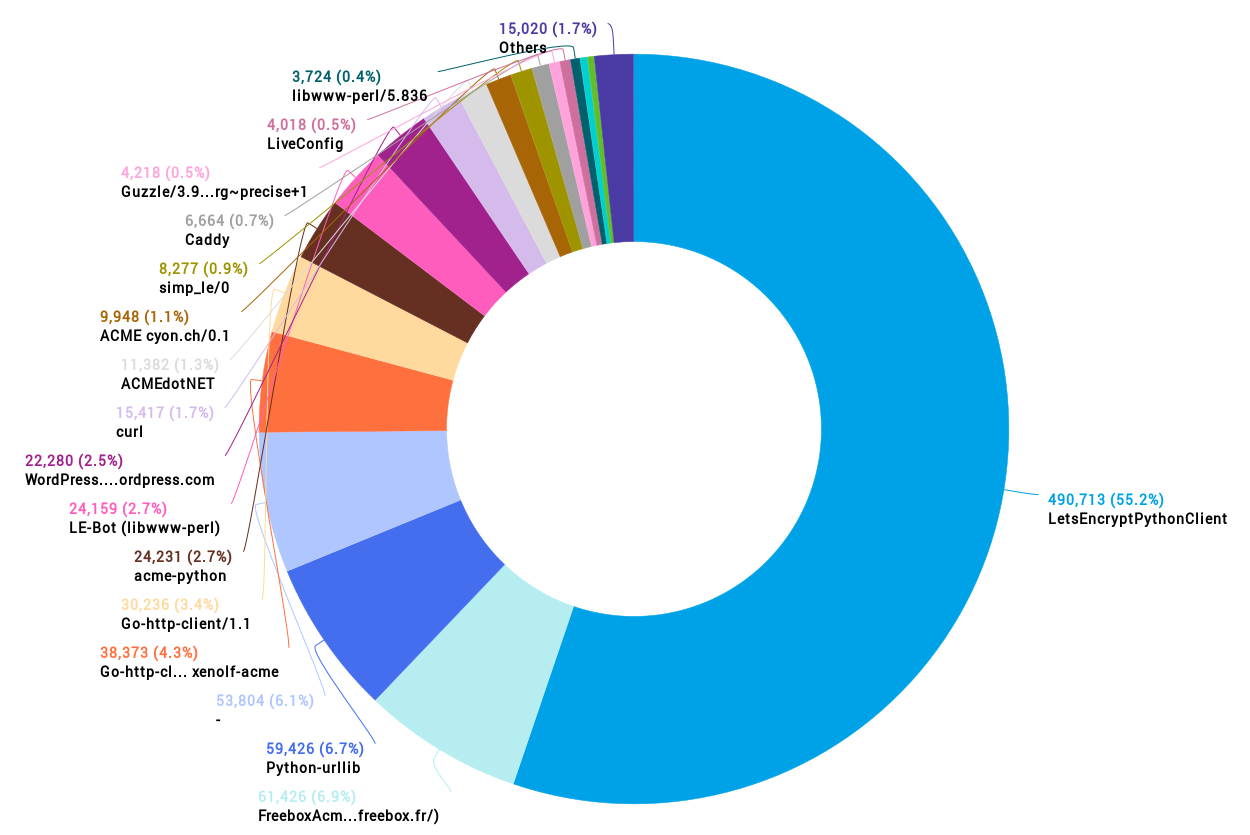
Let's Encrypt client distribution since Public Beta launch
All ACME clients are designed to obtain certificates from Let's Encrypt (or other CAs that might choose to use ACME). Our client goes a little further, with the option to install certificates in a wide range of web server software, and help admins get the security settings for their systems right. In the short run, the 0.5.0 and 0.6.0 releases will prioritize offering elegant hooks for OS packages to offer fully automated renewal and shipping the first version of our Nginx integration plugin.
Later in 2016, we'll be working to help web developers with a number of the other tasks that currently make correct TLS deployment very difficult, including detection and mitigation of mixed content problems; detecting when sites are ready for an HSTS header and offering to deploy one gradually; offering realtime mitigation against TLS vulnerabilities like Heartbleed, BEAST, CRIME, Logjam, DROWN, etc (at the moment, the client enables good TLS settings when a cert is first installed in Apache, but doesn't support changing them when best practices change); and expanding support to install certificates and offer security enhancements to popular email server software.
Thanks to everyone who has helped to make the launch of Let's Encrypt such a success; we hope that both the server and client projects continue to produce spectacular results in 2016.
- 1. Let's Encrypt includes many sub-projects. There's a serverside codebase called boulder that has been written largely by EFF and Mozilla staff and contractors, though ISRG is now beginning to hire its own engineering team; there's an operations team at ISRG that actually keeps Let's Encrypt's servers running; there's the client, which was written primarily by EFF and open source contributors, with some great packaging assistance from Mozilla; and ACME protocol which was designed by Mozilla, UMich and EFF engineers. Aside from hosting the renamed client project, EFF will continue to provide substantial organizational support for ISRG and engineering resources for the Let's Encrypt server code and the ACME protocol.