After Edward Snowden leaked NSA slides in 2013, two names became synonymous with the agency’s vast online spying powers: Upstream and PRISM.
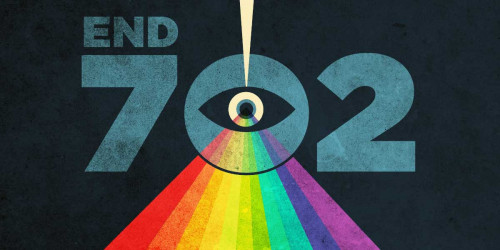
Those two types of surveillance work in different ways but pose similar threats to the privacy of Internet users around the world, including innocent Americans. Both also fall under a surveillance authority known as Section 702 , a provision of law that was enacted by the FISA Amendments Act of 2008 and is set to expire at the end of 2017.
In early 2017, the intelligence community rebranded these two kinds of surveillance, referring to them as “upstream” and “downstream.”
The names may have changed, but the surveillance is the same. Upstream surveillance involves collecting communications as they travel over the Internet backbone, and downstream surveillance (formerly PRISM) involves collection of communications from companies like Google, Facebook, and Yahoo.
In both upstream and downstream surveillance, the intelligence community collects and searches communications it believes are related to “targeted selectors.” It can target any foreign person located abroad who is believed to possess “foreign intelligence information.” Intelligence agencies use a secret and broad definition for “foreign intelligence information” that has, in the past, included things like information about foreign affairs. With a definition that broad, the intelligence community could easily target groups of people like journalists reporting on foreign governments or entrepreneurs working to expand their businesses to new countries.
In both upstream and downstream surveillance, the intelligence community searches for communications that are to or from “selectors,” or identifiers believed to be linked to foreign intelligence targets. Selectors can be specific things like email addresses, but they can also be much broader.
In downstream surveillance, U.S. intelligence agencies go directly to companies like Google, Facebook, and Yahoo and force the companies to turn over communications to and from identified selectors, including communications between targets and Americans. The companies are then prohibited from telling their users that their data has been turned over to the government.
In upstream surveillance, the NSA’s partners like AT&T tap into the high capacity fiber optic cables that carry Internet traffic and copy all of the data flowing through those cables. EFF has long argued that this initial interception and copying is a seizure under the Fourth Amendment and should require a warrant.
The agency is then supposed to filter out any communications that are “wholly domestic,” or between Americans located in the U.S. Not only does that mean the agency keeps communications between Americans and individuals located abroad, the imperfect system will mistakenly keep wholly domestic communications as well.
Once it has supposedly filtered out wholly domestic communications, the NSA searches the remaining data to see if any communications are to or from identified selectors. The agency also used to search for communications that merely mentioned selectors outside the “to” or “from” fields, but this practice of “about collection” was so privacy invasive that the NSA was forced to stop doing it.
Any remaining communications or chains of communications that contain selectors in the “to” or “from” fields are kept in government databases for future searches that do not require a warrant, including so-called backdoor searches for Americans’ communications.
Through both upstream and downstream surveillance under Section 702—a law that relaxes constitutional and other privacy safeguards in the name of targeting foreign surveillance—the intelligence community gains access to Americans’ online communications that it would regularly need a warrant to access. Our fundamental legal protections, including the Fourth Amendment, demand more.
With Section 702 set to expire at the end of this year, lawmakers need to hear from their constituents who are concerned about the privacy invasions they suffer under the law. Contact your representatives in Congress and tell them to use this looming sunset to rein in warrantless surveillance.