Encryption Isn’t Something We Can Negotiate About, No Matter How Politically Convenient That May Seem
Dear President Obama,
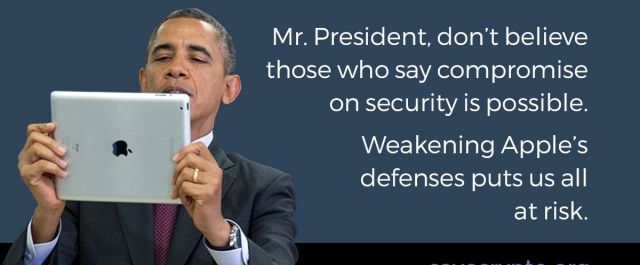
During your keynote conversation at SXSW, you called for a concession on security in our digital devices, stating that you don’t believe in “an absolutist view” when it comes to cryptography on phones.
We all want to find solutions to the problems of crime in our country and abroad, and technology can help us do that. Sometimes that means making compromises as a society. But reasonable people know that there’s one thing which isn’t subject to compromise: math.
The basic security of our digital devices is made possible because of a field of applied mathematics known as cryptography. In short, this means taking data and scrambling it so that it can’t be understood. If you want to unscramble the data, you need to have a unique key that will unlock it, unraveling the code and turning seemingly random characters into a clear message.
Cryptography is the foundation of information security throughout the digital world. It means that when you log into your email, you can read the messages — but other people can’t. We use crypto when we access our bank accounts, social networking sites, and documents stored in the cloud. Crypto safeguards our medical records, our location data, and the photos we send to our loved ones. The modern digital age and the Internet we have now were built atop the math of cryptography.
Today, mathematicians, engineers, and some of your own advisors are saying the same thing about the encryption debate: you can’t build a backdoor into our digital devices that only good guys can use. Just like you can’t put a key under a doormat that only the FBI will ever find.
This isn’t what certain career politicians and outspoken members of the Justice Department want you to believe. They’re searching for a quick-fix technical solution. They keep wondering why the engineering community can’t just find an answer. Even at SXSW you admitted that you didn’t have the expertise to design the kind of compromise you called for, where the encryption backdoors are magically secure and “accessible by the smallest number of people possible, for a subset of issues that we agree are important.” That’s because it’s not possible.
Too often, technical experts are ignored. Maybe it’s because they’re speaking in the dull realities of computer science and math. But as simple as the message may be, it’s still true: math can’t be negotiated away just because it’s inconvenient.
Any compromises we make in the security of our systems are compromises that can and will be exploited by those who would seek to do us harm. This includes malicious hackers, identity thieves, authoritarian governments, and corporate rivals. Your own Defense Department has identified insecure devices and networks as a key threat to our nation’s cybersecurity.
There are people whose lives are literally at risk who depend on the security of their phones: domestic violence victims, law enforcement agents, investigative journalists, judges, and those working for change in authoritarian regimes. But mostly, encryption protects hundreds of millions of regular people, who may not have anything to hide but don’t want their private lives exposed or their identities stolen because of lost or stolen smartphones, security flaws, and data breaches.
We’ve seen all too well the perils of imperfect security in Apple’s systems. In 2014, Apple suffered a major security breach in iCloud that resulted in a hacker accessing and publishing nude photos of celebrities like Jennifer Lawrence, Kate Upton and Ariana Grande. And while celebrities may have gotten the most press attention, the data breach could have affected anyone with an iPhone. It’s no surprise Apple sought to improve its security in the years since; its customers understood their personal lives were at stake.
Many of your advisors and former government officials know that vulnerabilities in our computer systems pose serious threats to our national security. Last year, millions of government workers and their families faced exposure of their most personal information when the Office of Personnel Management was breached, and the federal government is expected to spend half a billion dollars cleaning up in the wake of data breaches in the next few years. The OPM hack is just one in a series of high-profile breaches where extraordinarily sensitive information was stolen. The experts have been telling you that, faced with these challenges, we need to strengthen cryptography, not undermine it.
We’ve also seen the ramifications of bad policies that tried to weaken security. In the 1990s, there was a concerted effort by certain outspoken law enforcement officials to weaken our cryptography and insert backdoors into our systems. Last year, university researchers discovered how these policies have had long-term, unintended consequences: weakened security persisted in our software for decades. The researchers demonstrated that this resulted in massive, ongoing vulnerabilities in thousands of Internet services. We still don’t know how many millions of people’s personal communications were put at risk because of these shortsighted policies.
The public debate we’re having over the security of our devices boils down to a question of math versus politics.
On the one hand, we have academics, security engineers, and mathematicians explaining that encryption isn’t something we can negotiate away. On the other side of the debate, we have those who want an easy answer. We’re confronted with crypto-critics like FBI Director James Comey, the attorney general, and others whose expertise in criminal investigations doesn’t prepare them to appreciate the technical ramifications of what they are proposing. However well-meaning, they’re seeking to take advantage of recent tragedies to advance a course that could undermine the security of all of us.
President Obama, we need to let facts and reason win the day. That means standing up for math, even if it’s not politically popular. Please respond to the 100,000+ people who have called on you to oppose backdoors through savecrypto.org, and let security be your legacy.
Crossposted on Medium. Updated to clarify the type of security breach Apple suffered in 2014.