ESET researchers recently discovered a false “trojanized” version of Tor Browser that collectively stole $40,000 USD in Bitcoin.
This does not mean that Tor or Tor Browser itself is compromised in any way. It only means that attackers found a new, insidious way to create and distribute a fake version of the Tor Browser. In this case, attackers also faked EFF’s own HTTPS Everywhere extension using a modified manifest.json file with a few settings changes. The attackers used a fake HTTPS Everywhere extension in their campaign because Tor does in fact package the HTTPS Everywhere and No Script extensions into its browser. Including details like normal extensions in the trojanized version of Tor could prevent eagle-eyed users from catching red flags that indicate they’re using a fake browser.
Nefarious HTTPS Everywhere Code
The manifest.json file in web extensions states explicit permissions and scope of activity the web extension will commit. In this attack, this modified file widened the scope by adding content scripts. This allows the extension to load scripts into the browser and potentially modify what the user sees and interacts with on various web pages.
Left: Real manifest.json Right: Fake manifest.json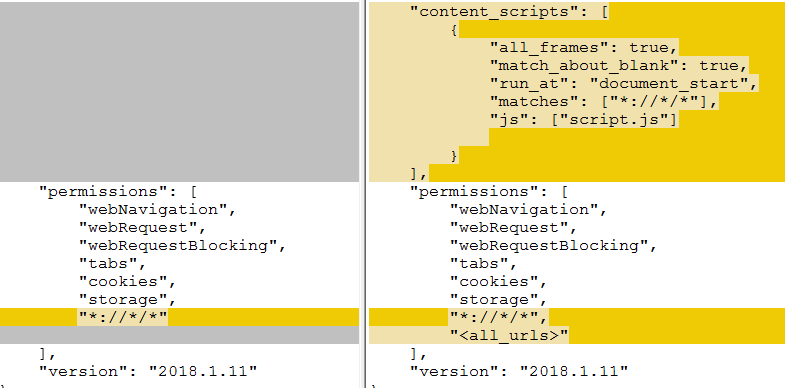 Photo Credit: https://www.welivesecurity.com/2019/10/18/fleecing-onion-trojanized-tor-browser/
Photo Credit: https://www.welivesecurity.com/2019/10/18/fleecing-onion-trojanized-tor-browser/
In this case, this content script notified the attacker's C&C (Command and Control) server and in return loaded further scripts that modify the user's experience: in this case, changing wallet addresses on the commonly used Russian money transfer service QIWI, or on Bitcoin wallets located on various Darknet markets.
Trojanized Tor Browser
This malicious download of Tor is older (version 7.5) with its xpinstall.signatures.required settings set to false, which disables a digital signature check for installed Tor Browser add-ons and bypasses the HTTPS Everywhere signature check.
This modified version of the Tor Browser targeted Russian-speaking users and presented them with “out of date” warnings. This prompted some to click a button to “update” to the trojanized Tor browser at the fake domains tor-browser[.]org and torproect[.]org. (The authentic domain is torproject.org.)
Researchers discovered advertisements promoting the fake Tor Browser in spam messages on Russian forums, covering topics such as darknet markets, cryptocurrencies, internet privacy and censorship circumvention. The advertisements falsely promised to help users bypass CAPTCHA and Roskomnadzor, a Russian censorship body in media and telecommunications.
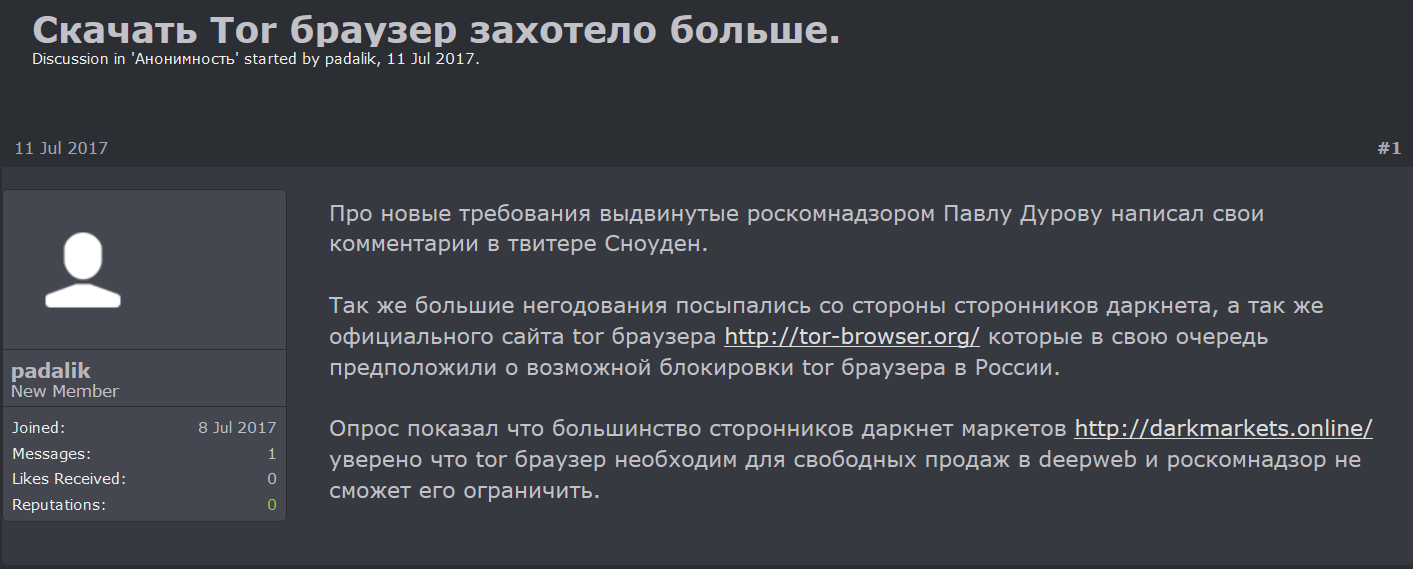 Photo Credit: https://www.welivesecurity.com/2019/10/18/fleecing-onion-trojanized-tor-browser/
Photo Credit: https://www.welivesecurity.com/2019/10/18/fleecing-onion-trojanized-tor-browser/Spam message promoted in Russian Forums
The most insidious part of these advertisements was tricking people into believing that the trojanized Tor Browser would guarantee anonymity. In fact, the attackers behind this trojanized Tor Browser set a unique identifier in the modifications: a custom user-agent, a text-based identifier that allows other hosts to see what software and operating system the user has. So even though the real Tor proxy was still present in this browser, ultimately anonymizing user’s I.P. addresses, this custom user-agent allowed the attackers to create and track a very specific fingerprint on their victims. That also means that any victims using this malicious browser could still be fingerprinted and tracked by a myriad of other observers.
Conclusion
This campaign relied on the user not catching a few red flags that indicate a potentially fake or malicious Tor Browser but are easy to miss. Some of these red flags include:
- Fake domains for downloading Tor browser
- Unverified signature for the download
- Outdated Tor Browser version
- Non-AMO (Mozilla Add-ons Store), unverified HTTPS Everywhere extension
- Modified scope of HTTPS Everywhere permissions and activity
- Likely no NoScript extension present to block Javascript (Assumed from report)
Even though this was a targeted, atypical attack, it may still concern some users. With these red flags in mind, here are some tips and helpful links to ensure you are using the proper Tor Browser:
- What is the current version of Tor?
- At the time of this post, 9.0.
- The official, up-to-date Tor Browser is available at this address: https://www.torproject.org/download/
- Distribution directory: https://dist.torproject.org/torbrowser/
- To verify Tor downloads: https://support.torproject.org/tbb/how-to-verify-signature/
- What is the proper way to update Tor?
- Please reference this page: https://tb-manual.torproject.org/updating/
- Tor also normally announces updates via their blog: https://blog.torproject.org/new-release-tor-browser-90
- Which add-ons are allowed in Tor currently?
- At the time of this post, the only add-ons bundled with Tor are the HTTPS Everywhere and No Script extensions. Installing any other add-on could de-anonymize you.





