Since March of this year, EFF has reported extensively on the ongoing campaign to use social engineering to install surveillance software that spies on Syrian activists. Syrian opposition activists have been targeted using several Trojans, including one disguised as a Skype encryption tool, which covertly install spying software onto the infected computer, as well as a multitude of phishing attacks which steal YouTube and Facebook login credentials.
As we've tracked these ongoing campaigns, patterns have emerged that links certain attacks to one another, indicating that the same actors, or groups of actors are responsible. Many of the attacks have installed versions of the same remote access tool, DarkComet RAT, and reported back to the same IP address in Syrian address space. The latest attack covertly installs a new remote access tool, Blackshades Remote Controller, whose capabilities include keystroke logging and remote screenshots. Evidence suggests that this campaign is being carried by the same pro-Syrian-government hackers responsible for the fake YouTube attack we reported in March, which lured Syrian activists in by advertising pro-opposition videos, stole their YouTube login credentials by asking them to log in before leaving a comment, and installed surveillance malware disguised as an Adobe Flash Player update.
This malware is distributed via Skype. It is distributed in the form of a “.pif” file. This sample was sent via the compromised Skype account of an officer of the Free Syrian Army. In the conversation shown in the screenshot below, a malicious link is sent claiming to be an important new video. Two hours later his friend asks the officer if his account is ok. The officer replies that his account was compromised and this link sent out to various people from his address book.
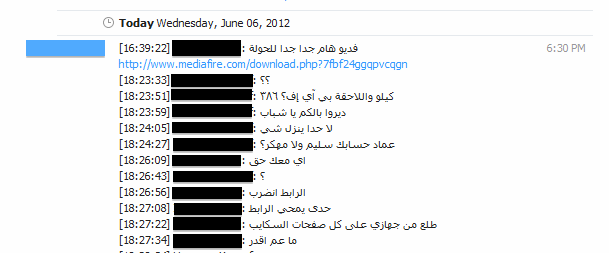
Clicking on the link downloads a file called "new_new .pif." For those who would like to make sure that they have the correct sample of this malware, the md5sum is 0d1bd081974a4dcdeee55f025423a72b.
On execution, the following files are dropped:
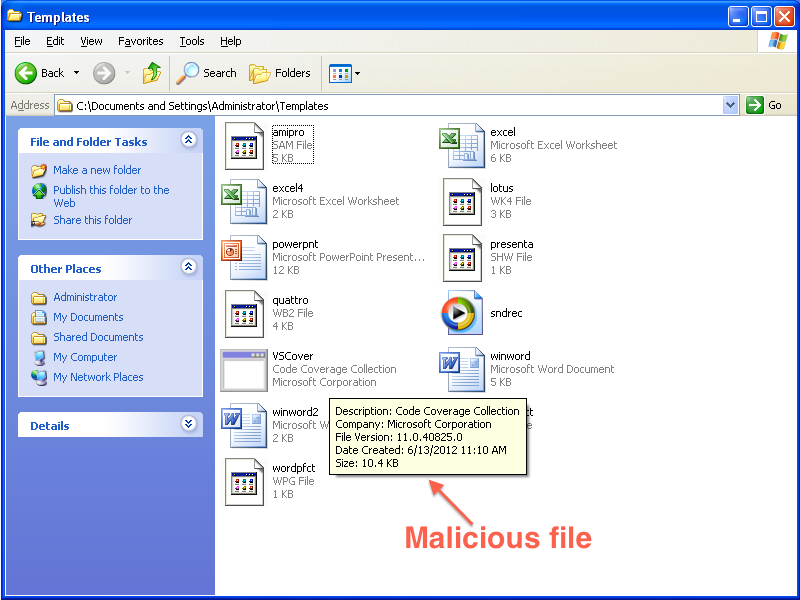
C:\Documents and Settings\Administrator\Templates\VSCover.exe
Shown in the screenshot below:
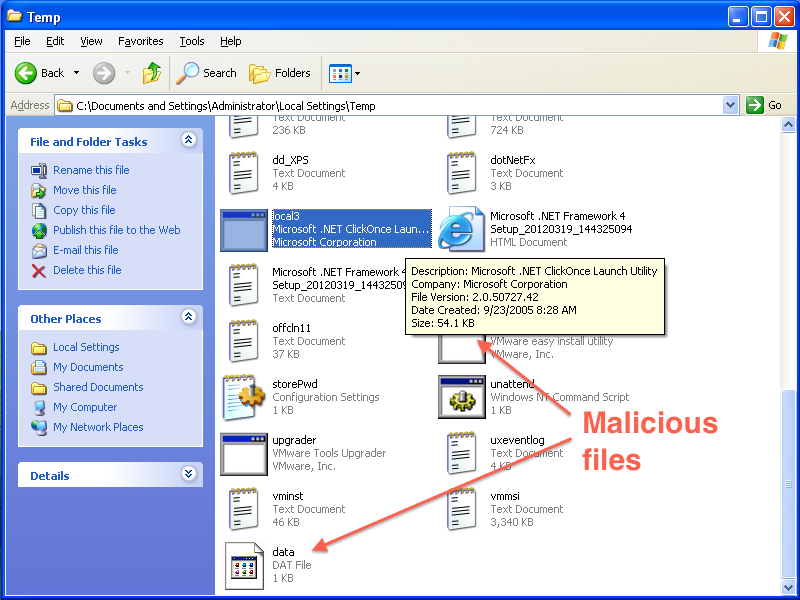
C:\DOCUME~1\ADMINI~1\LOCALS~1\Temp\local3.exe
C:\DOCUME~1\ADMINI~1\LOCALS~1\Temp\data.dat
Shown in the screenshot below:
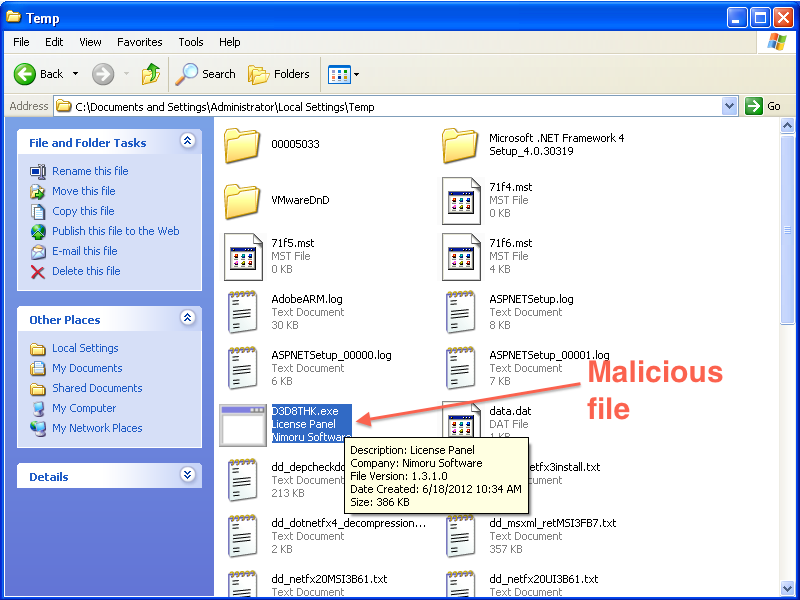
And C:\Documents and Settings\Administrator\Local Settings\Temp\D3D8THK.exe
Shown in the screenshot below:
If you see these files on your computer, you have been infected with BlackShades RAT. If your computer is infected, deleting the above files or using anti-virus software to remove the Trojan does not guarantee that your computer will be safe or secure. This malware gives an attacker the ability to execute arbitrary code on the infected computer. There is no guarantee that the attacker has not installed additional malicious software while in control of the machine.
Some anti-virus vendors recognize Blackshades RAT. You may try updating your anti-virus software, running it, and using it to remove the Trojan if it comes up, but the safest course of action is to re-install the OS on your computer and change the passwords to any accounts you have logged into since the time of infection.
EFF urges Syrian activists to be especially cautious when downloading files over the Internet, even in links that are purportedly sent by friends. As members of the Syrian opposition become more savvy in using encryption, satellite networks, and other tools to evade the Assad regime's extensive Internet surveillance capabilities, pro-Syrian-government malware campaigns have increased in frequency and sophistication. For Syrian activists, poor security practices can have potentially disastrous consequences.
For a detailed technical analysis, please see this blog post from Citizen Lab.