By the time you read this, Let’s Encrypt will have issued its 12 millionth certificate, of which 6 million are active and unexpired. With these milestones, Let’s Encrypt now appears to us to be the the Internet’s largest certificate authority—but a recent analysis by W3Techs said we were only the third largest. So in this post we investigate: how big is Let’s Encrypt, really?
What are certificate authorities, and how do you measure their size?
Certificate authorities (CAs) issue and maintain digital certificates that help web users and their browsers know they’re actually talking to the site they intended to. This is crucial to secure, HTTPS-encrypted communication, as these certificates verify the association between an HTTPS site and a crypographic public key. A CA provides the owner of a website with a signed certificate that web visitors can independently verify. The certificate tells a user’s browser software, “If you use this key to set up secure communications with this website, no one can intercept those communications.” Without such an introduction, browsers can succumb to traffic interception, modification and eavesdropping; even if they used encryption, they wouldn’t be sure if they were talking directly to a site as opposed to a man-in-the-middle attacker.1
Let’s Encrypt is a free, automated, open CA founded by EFF, Mozilla, and the University of Michigan, with Cisco and Akamai as founding sponsors. But is it the largest CA? It turns out this could mean several things: issuing the most public certificates, issuing the most active public certificates, protecting the most Internet connections or sites, or any of a host of other possible metrics. In this post we’ll walk through a couple of ways to measure this, and the limitations and caveats that comes with those measurements.
The numbers
At present, Let’s Encrypt has issued 6 million unexpired certificates for either 4 or 10 million domains, depending on how you count.
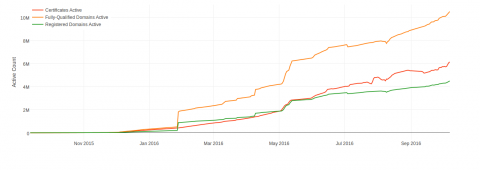
Source: JC Jones
On this chart, “certificates active,” in red, represents the number of certificates that have been issued and are not yet expired. 2
Some of these un-expired certificates are duplicates, with more than one certificate covering one domain name. Others are the opposite, covering many domain names under one certificate.3 So it's probably more accurate to look at the number of distinct domains covered by unexpired certs. “Fully-qualified domains active” in orange shows the number of different names among non-expired certificates. For example, www.eff.org and supporters.eff.org are treated as two different names. This metric can overcount sites; while most people would say that eff.org and www.eff.org are the same website, they count as two different names here.
Finally, “Registered domains active” in green counts the number of different top-level domain names among non-expired certificates. In this case, supporters.eff.org and www.eff.org would be counted as one name. This metric may undercount different sites, because pages under the same top-level domain still may be run by different people with different content—for example, different WordPress blogs hosted under wordpress.com.
Counting by number of certs: 3rd largest, or largest?
Our friends at W3Techs Web Technology Surveys recently released a blog post analyzing the CA market and putting Let’s Encrypt in third place among certificate providers.
When we looked closely at these numbers, however, we found that W3Techs was not looking at the entire certificate market; its analysis took into account only the top 10,000,000 most popular websites (as ranked by Alexa). This is important because Let’s Encrypt (below shown as “IdenTrust,” because of the root Let’s Encrypt uses) is commonly used by smaller, less popular, low-traffic sites rather than big, popular ones. For that reason, W3Tech’s third-place ranking that relied on the biggest, most popular sites on the web enormously undercounted Let’s Encrypt’s overall market share. The smaller sites that we primarily serve are exactly the sites that W3Techs (and other analyses of top Alexa-ranked sites) are least likely to count.
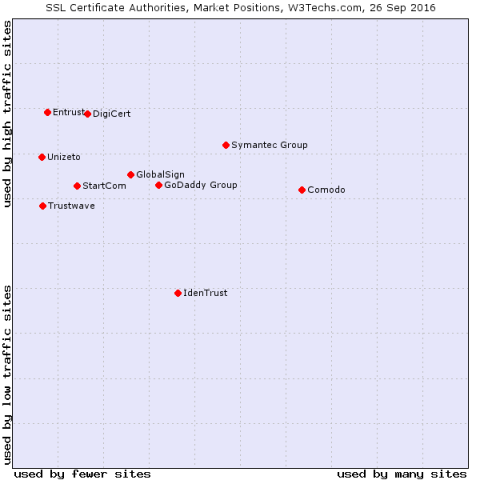
CAs in the lower part of the graph tend to serve more low-traffic sites. Source: W3Techs.
By other metrics, Let’s Encrypt is in fact the CA that has issued the most certificates and protected the most sites. This ranking from the Censys project looks at all known certificates that are valid, unexpired, and would be accepted by browsers at the moment of the query:
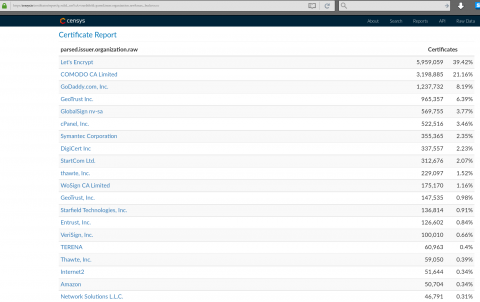
Source: censys.io.
But this first-place ranking requires some caveats. The rankings above include data from Certificate Transparency, an open-source effort to monitor and audit TLS/SSL certificates. This data may include certificates that were never deployed in practice or are no longer actively in use. So, if someone gets a Let’s Encrypt certificate but then doesn’t actually use it, it still contributes to Let’s Encrypt’s first-place spot in the chart above.
This dataset may also include duplicates. For example, a webmaster new to TLS/SSL certificates may accidentally run a Let’s Encrypt client like Certbot five times in a row and get the same certificate every time. This will show up in the chart above as five different certificates, even though that webmaster is probably only using one. Of course, this is counteracted by the fact that many other certificates cover multiple domains at once.
Lastly, there are categories of certificates that aren’t being counted here. This ranking covers only publicly trusted certificates (as opposed to self-signed ones, or those signed by private CAs not trusted by browsers by default) for domain names (as opposed to, for example, S/MIME certificates for email addresses, of which there are a huge and largely unmeasured number).
Valuable contributions regardless of numbers
The biggest caveats in the two rankings above—whether the dataset takes into account less popular sites (which makes the W3Techs numbers very pessimistic about Let’s Encrypt), and the possibility of unused or duplicate certificates (which may make our own numbers optimistic)—illustrate Let’s Encrypt’s valuable contributions to encryption efforts regardless of numbers or rankings.
As the difference between the two datasets shows, Let's Encrypt has been adopted more by smaller sites than by larger ones—often personal blogs or by the sites of small businesses and associations. That means that, compared to other CAs, we protect fewer of the most famous and most popular Internet sites, and apparently also a smaller fraction of all web browsing activity. But that's fine by us.
One of the ways Let's Encrypt has been helping to secure the web is by making it easy and affordable for sites that have never had certs before to turn on secure HTTPS connections, and for software systems to start enabling HTTPS automatically and by default. Our free certificates may be more likely to be left unused than expensive certificates, and less expert webmasters may accidentally duplicate certificates—but that’s part of making HTTPS integration available to more webmasters across a range of resource and skill levels. Statistics suggest that most of our growth has come not at the expense of other CAs, but from giving previously unencrypted sites their first-ever certificates.
Rankings also fail to capture the communities that a CA like Let’s Encrypt can serve. A large share of Let’s Encrypt certificates have been issued to major hosting companies and platforms, including: Automattic, the web development corporation behind WordPress.com; Shopify, an e-commerce platform; and OVH, a European ISP. And they are not alone. Dozens of web hosting providers and companies have made the commitment to use Let’s Encrypt to automatically protect their customer sites with HTTPS.
We are committed to supporting more companies and communities who want to make this move. Learn more about Let’s Encrypt and how to use the web’s largest CA here.
- 1. Note that certificates don’t really solve the related authentication puzzle of knowing that you’re visiting the right domain name and are not being phished, which is in many ways a harder problem.
- 2. Although it is not shown on this chart, our count of all certificates ever issued, including expired certs, is about 12 million.
- 3. Let's Encrypt supports up to one hundred domains per certificate.



