Much has changed in the nearly ten years since we launched our first lawsuit challenging the NSA’s illegal surveillance of millions of Americans’ Internet communications. Over time, the defendants in the cases have changed; the legal “authority” the government has invoked to justify the program has changed; and the public’s knowledge and understanding of the programs has increased remarkably.
But, nearly a decade in, one thing has stayed remarkably constant: the relevant facts. The NSA, with the help of the nation’s largest telecommunications firms, like AT&T, has tapped the nation’s Internet backbone, searching and sifting through vast amounts of innocent Americans’ Internet communications.
This was true when we filed our first lawsuit challenging the NSA’s programs in 2006, and it’s still true today. And, as new NSA slides published in August by Pro Publica and the New York Times confirm, even in 2006, we were remarkably accurate in our description of how the NSA’s program operates.
In fact, we even got the diagrams right.
Below is an image of a diagram we filed in 2006 in our case, Hepting v. AT&T—our first case challenging NSA surveillance. The diagram, created by our expert J. Scott Marcus, charts the operation of the surveillance installations at an AT&T facility in San Francisco. The declaration and diagram were based on information provided to us by whistleblower Mark Klein. We've subsequently relied on this declaration in our ongoing case, Jewel v. NSA, too.
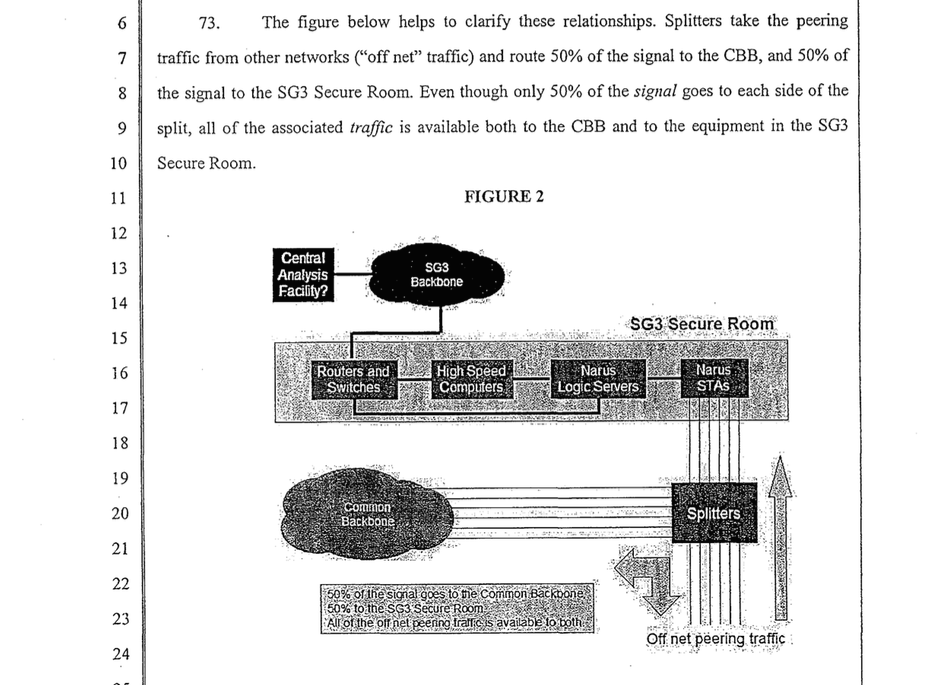
A graphic depicting NSA Internet surveillance, originally created and used in Hepting v. AT&T
As the diagram shows, the NSA’s Internet surveillance program operates at key junctures along the “common [Internet] backbone,” the high-capacity fiber optic cables connecting large portions of the domestic Internet infrastructure. The diagram shows splitters, installed at these junctures, that copy and divert AT&T’s “peering traffic”1 to a secure room containing technology—a packet sniffing device and other routers—for searching and sifting the traffic. The traffic is then sent, through a secure line, to a “central analysis facility.”
Now, compare our decade-old diagram with the newly released, internal NSA dataflow diagram showing how one of the NSA’s Internet content surveillance programs operates. The similarities are remarkable.
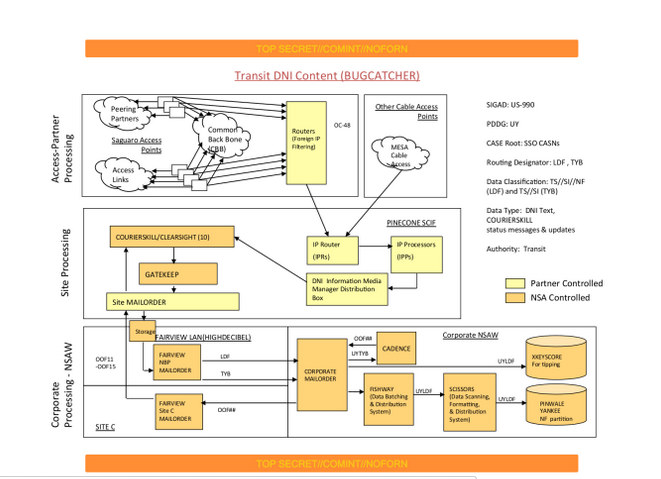
An internal NSA graphic depicting NSA Internet surveillance
The first box, in the top left of the diagram, describes NSA’s “Access-Partner Processing.” The “partner” providing access here, as reported by the NY Times and Pro Publica, is AT&T. At the “Saguaro Access Points,” splitters copy and divert traffic — traffic from AT&T's “peering partners" on its path to the “Common Back Bone”— to a series of routers where the traffic is sorted and searched. Following some initial filtering, the traffic is then sent to a central “Site Processing” facility—the PINECONE SCIF. (A “SCIF,” which stands for Sensitive Compartmented Information Facility, is a secure location used to process classified information). The diagram then goes on to describe further processing and storage of the traffic within NSA’s facilities.
Compared side-by-side, both diagrams show: (1) AT&T's peering traffic; (2) copied by splitters; (3) on its path to the common backbone, which enables (4) initial, on-site searching and analysis of that traffic; and (5) the transmission of that traffic to a central processing facility for further analysis.

The relevant portions of the two graphics, side-by-side. To highlight the similarities between the two diagrams, we rotated and inverted our original graphic and cropped the relevant portion of the NSA's graphic.
Those facts form the foundation of our ongoing lawsuit, Jewel v. NSA, challenging the constitutionality of the NSA’s domestic surveillance program. We distilled those critical facts, in slightly different terms, in yet another graphic we submitted to the court last year:

Despite the overriding similarity between our factual allegations—public now for nearly a decade—and the government’s own description of the NSA’s surveillance program, the government continues to insist that the details of the NSA’s operation remain a state secret. Based on those claims, a judge dismissed Jewel earlier this year.
But there are limits to the government’s ability to play ostrich—to stick its head in the ground and pretend like the world does not already know that AT&T is facilitating its Internet surveillance program. As one Court of Appeals recently put it, the courts should not “give their imprimatur to a fiction of deniability that no reasonable person would regard as plausible. There comes a point where . . . Courts should not be ignorant as judges of what [they] know as men and women."
We are at that point with AT&T and the NSA’s upstream surveillance program. It’s time for the government to come clean about its collaboration with AT&T, and it’s time for the public, adversarial courts to decide the constitutionality of the NSA’s surveillance program. We appealed the district court’s dismissal of our case, and we’re hopeful the court of appeals will agree with us.
- 1. “Peering” refers to the process where two (or more) providers agree to accept and exchange traffic for their respective customers. So, for example, the location where AT&T’s traffic is exchanged with Sprint’s traffic is called a “peering link,” and AT&T and Sprint, in this example, are “peering partners.”



