A few weeks ago, we started seeing reports of a Trojan called Darkcomet RAT on computers belonging to Syrian activists which would capture webcam activity, disable the notification setting for certain antivirus programs, record key strokes, steal passwords, and more--and send that sensitive information to an address in Syrian IP space. Symantec's writeup and recommendations are available here.
Now we've seen reports of new malware, Xtreme RAT, which sends data back to the same address in Syrian IP space and whose release appears to predate the Darkcomet RAT Trojan. Reports indicate the Trojan is being spread through email and chat programs. The malware was used to log keystrokes and take screenshots of the victim's computer, and it is likely that other functionality was also used.
You should take steps to protect yourself from being infected by not running any software received through e-mail, not installing software at all except over HTTPS, and not installing software from unfamiliar sources even if recommended by a pop-up ad or a casual recommendation from a friend. EFF also recommends keeping your computer's operating system up-to-date by immediately installing security updates from their operating system vendor. Do not use an operating system that is obsolete and no longer getting security updates.
Finding any of the following files or processes is an indicator that your computer has been compromised by Xtreme RAT. More indicators are a stronger sign of compromise.
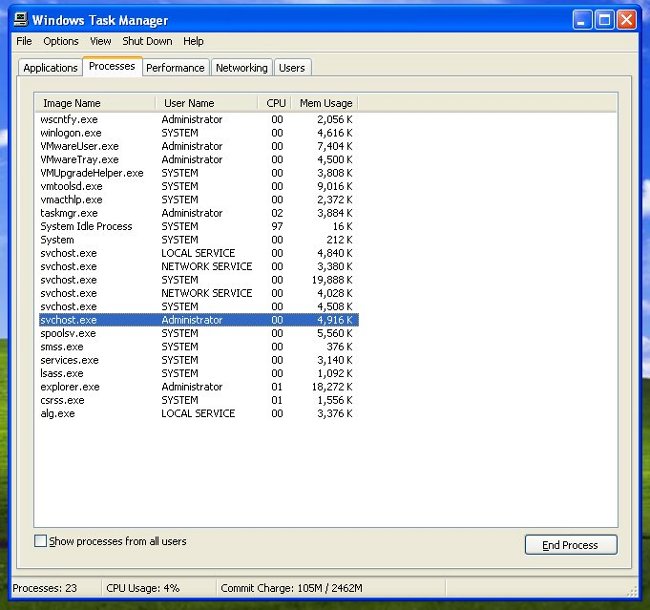
How to identify Xtreme RAT if it is running on your computer, if you are running Microsoft Windows:
1. Go to your Windows Task Manager by pressing Ctrl+Shift+Esc and click on the Processes tab.
Look for a process called svchost.exe running under your username. In this example, the user is Administrator.
2. Open your Documents and Settings folder. Click on your username (in this example, "Administrator"). Click on "All Programs." Click on "Startup." Look for a link labeled "(Empty)", which is a sign of infection.

3. Open your Documents and Settings folder. Click on your username (in this example, "Administrator"). Open the Local Settings folder. Open the Temp folder. Look for two files: _$SdKdwi.bin and System.exe. If "display file extension" is on the file will appear as System.exe. If it is off, it will display as System Project Up-date DMW.

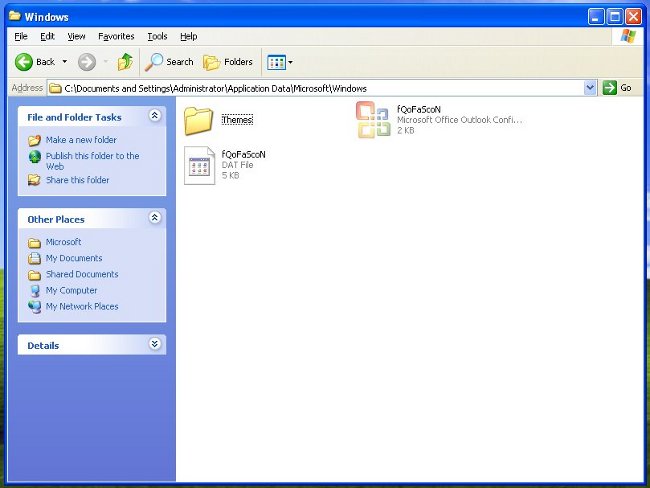
4. Open your Documents and Settings folder. Click on your username (in this example, "Administrator). Open the Local Settings folder. Open the Application Data folder. Open the Microsoft folder. Open the Windows folder. Look for two files: fQoFaScoN.dat and fQoFaScoN.cfg.
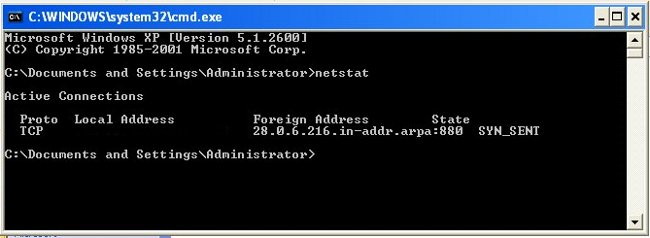
5. Click the Start button. Type "cmd" to open a command window. Type "netstat". In the resulting list of active connections, look for an outbound connection to the following IP address: 216.6.0.28.
What To Do If Your Computer is Infected:
If your computer is infected, deleting the above files or using anti-virus software to remove the Trojan does not guarantee that your computer will be safe or secure. This malware gives an attacker the ability to execute arbitrary code on the infected computer. There is no guarantee that the attacker has not installed additional malicious software while in control of the machine.
As of March 6, 2012, there is only one anti-virus vendor which recognizes this Trojan. You may try updating your anti-virus software, running it, and using it to remove the Trojan if it comes up, but the safest course of action is to re-install the OS on your computer.