2008 was another tough year for proponents of digital rights management (DRM). As we have pointed out in years past, the infamous Darknet assumptions — three big reasons that DRM copy protection will never work, as set forth in 2002 by a team of Microsoft engineers — continue to be proven true by events.
Let's review the three Darknet assumptions one at a time, and see how they fared in 2008.
1. Any widely distributed object will be available to a fraction of users in a form that permits copying.
2008 may be remembered as the year online music went DRM-free. But other industries remain enamored with DRM, and in 2008 their customers continued to circumvent copy protections and make unauthorized copies for free.
When the PC game Spore was released, fans were outraged to find the program installed a separate program called SecuROM intended prevent copying of the game, and many protested by quickly posting cracked versions of the game. Spore soon became the most pirated game on the Internet — no surprise, since most new games are available almost immediately for free over P2P sites. Some users say downloading cracked copies is the only way the games will play properly on their systems.
Meanwhile, DVD ripper software remains popular (despite Hollywood's attempt to sue the software makers out of business). Even the supposedly unbreakable Blu-ray and DVD-HD DRM was easily cracked — twice in 2008 — by SlySoft.
And for all the effort that the rightsholders' lobby to restrict regular consumers' technology, what are the most sought after, and therefore most widely-distributed infringing files on underground sites? Screener DVDs, pristine copies of currently showing films which emerge from Hollywood itself.
2008 also saw a rise in the sharing of expensive textbooks online, showing that with enough incentive (and a lack of convenient ebook equivalents), individuals will spend hours scanning, OCRing and correcting thousands of physical printed pages.
2. Users will copy objects if it is possible and interesting to do so.
P2P filesharing continued to grow in popularity in 2008, and even showed signs of joining the mainstream. Pirate Bay claimed to be the world's largest P2P network, with over 22 million users. Comcast claimed that vast amounts of P2P traffic was choking their networks (leading them to surreptitiously block BitTorrent traffic).
While it's hard to find accurate figures for P2P usage, there is no evidence that filesharing networks are declining, and anecdotal evidence suggests the opposite. An informal student poll cited by an LA Times Blog found that 64% of students enrolled in a media business course regularly download entertainment through unauthorized sources. 43% were "not concerned" about getting caught.
3. Users will share copies as long as they are connected by high-bandwidth channels.
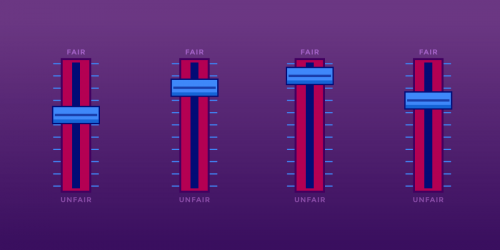
With the failure of DRM to prevent copying, and the continuing popularity of file sharing, that leaves only one way for the entertainment industry to try to prevent copying: filtering content at the point of connection to the Internet. That's why in 2008 we saw the RIAA and other industry voices dropping attempts to prosecute individuals and shifting towards calls for ISPs to filter content — as well as legislation with a similar purpose.
The rise of filtering may make sense to content industries, given the fact that the Darknet appears most vulnerable at point #3. But the filtering strategy relies on ISPs making a regular practice of inspecting packets coming across their networks, a practice that does not bode well for the right of privacy, as Professor Paul Ohm warned in a 2008 paper. ISP filtering will simply trigger a new privacy arms race, as users fortify their encryption methods and ISPs step up surveillance.
Then there is the worry that sharing of files could move off the net entirely. Already, the exponential increase in size and speed of digital storage is making it easier than ever for files to be traded outside of P2P networks, simply by passing flash drives hand to hand. ISP filtering could end up simply driving the Darknet further underground, making it harder than ever to track and monetize online sharing. As of January 2009, an external terabyte of storage costs around $180. Even relatively pessimistic estimates of the future cost of drives suggest that the terabyte drive will drop below $100 in the next three years. The next generation of file-sharers may be as likely to swap the entire corpus of modern music by hand as they will pick off individual songs online.
Like other attempts to stop digital files from doing what digital files do best — make copies — these attempts will do nothing to get artists, musicians or game designers paid. As EFF and others have been arguing for years, the relative ease of copying digital information is a fact of life in the digital world. Attempts to prevent widespread copying are doomed to failure. Rather than make criminals out of fans, we can work to create systems that help get artists paid while delivering content to more homes than ever before. That's a better way forward.