Yesterday we filed a motion for partial summary judgment in our long running Jewel v. NSA case, focusing on the government's admitted seizure and search of communications from the Internet backbone, also called "upstream." We've asked the judge to rule that there are two ways in which this is unconstitutional under the Fourth Amendment:
- The admitted seizure of communications from the Internet backbone, for which we have government admissions plus the evidence we received long ago from Mark Klein.
- The government's admitted search of the entire communications stream, including the content of communications.
We're very proud of this motion (especially the infographic), and we're hoping that this shifts the conversation around the world to how the surveillance actually happens, rather than the U.S. government's self-serving word games about it.
As this motion progresses, here are a few points to keep in mind:
1) Government Admissions: This motion is based almost entirely on the government's formal, acknowledged admissions. This is because a Motion for Partial "Summary Judgment," such as this one, cannot be decided if the parties disagree about material facts. It is a common litigation strategy to make a motion based upon the undisputed facts so that the court can rule on an important legal issue, even if there are other facts that are not yet agreed upon.
In essence, we are saying that even if you accept the government's own descriptions of its internet backbone spying, the spying is still unconstitutional. You can see which formal government statements we're relying on at pages 4-9 of the motion, some of which are directly attached in the Declaration of Richard Wiebe.
That doesn't mean that EFF thinks that the government's current description is correct or complete about what they are actually doing. We've watched the government play fast and loose with the facts—and even outright lie to Congress—too many times for that. In this case, many careful watchers of the government believe that the government isn't actually filtering out some wholly domestic traffic—stage 2 in our brief—or at least isn't doing it in the way it says it is. But because to win this motion we do not need the judge to decide whether the government is telling the truth about the filtering, we have included stage 2 in our description. Our argument is that the government's searching violates the Fourth Amendment even if stage 2 occurs.
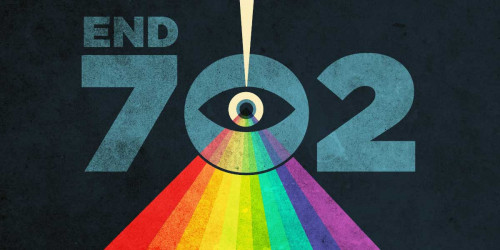
2) Domestic backbone only: This motion is based on the domestic backbone surveillance as it has been described in the government's released documents, including Foreign Intelligence Surveillance Court opinions. This is what the government sometimes calls "upstream" and claims is allowed by FISA Amendments Act section 702 (50 USC 1881a). To be clear, this motion does not address other areas of government mass surveillance. For example, we know that the government also conducts sweeping mass collection outside of the United States of both Americans' and foreigners' communications under Executive Order 12333 as well as other kinds of surveillance inside the U.S. This motion is just about the Fourth Amendment violations due to domestic surveillance through tapping into the Internet backbone.
Note also that EFF does not think section 702 of the FISA Amendments Act actually authorizes the backbone collection. Section 702 says nothing about mass seizure and searches, much less authorizes them. But in any event, the orders of the FISC issued under section 702 are not the warrants that the Fourth Amendment requires—so the technique is unconstitutional even if 702 applies.
3) Backbone collection isn't just at the telecommunications "border": One reason that many people, including our expert J. Scott Marcus, don't believe that the government is simply searching through international or foreign-to-foreign communications when it engages in backbone collection is that those collections aren't just happening at the US "border" for communications. The "border" for these purposes would be where the undersea fiber optic cables come up out of the ocean and satellite links come down into the country. For example, none of the undersea cables land in San Francisco, as shown by these maps: Transpacific Cable Landings: Western US, which is a blow up of this cool interactive map. Nor, according to expert analysis, would it be the right location to intercept satellite feeds into and out of the country. Meanwhile, a screenshot of a Snowden slide from a Brazilian news report shows that the government has a large number of collection points in the US heartland, far from any international border.
There are lots of other reasons to be skeptical of the government's claims, but our point in the motion is that even if they are limiting their searches to communications that cross the border, the searches are still unconstitutional. This is because they admittedly includes Americans' communications when they speak to someone abroad or access a website hosted abroad, something we talk about on pages 6-8 of the motion and also again on pages 19-20 in footnote 22.
4) Word games to watch out for: As we try to make clear in the motion, especially at footnote 13, the government uses a very different definition of "collect" or "acquire" than most people do, limiting "collection" or "acquisition" to stage 4, when the communications are actually stored in the government's database. An easy place to see this is in DNI Clapper's explanation for denying to Senator Wyden that the U.S. government is “collecting” data on millions or hundreds of millions of Americans. Clapper told NBC's Andrea Mitchell: “[T]here are honest differences on the semantics when someone says ‘collection’ to me, that has a specific meaning, which may have a different meaning to him [Senator Wyden].” DNI Clapper's position is not new. A 1982 Department of Defense manual says that information is considered to be collected only after it has been “received for use by an employee of a DoD intelligence component,” and that “[d]ata acquired by electronic means is ‘collected’ only when it has been processed into intelligible form,” without regard to when the information was initially acquired by a surveillance device.
These are just four things that may help you keep track of the discussion as this fight continues.