As Sunshine Week rolls on, we wanted to highlight EFF’s transparency work over the past year. In an era of excessive government secrecy, the FOIA process is becoming increasingly vital to both keeping the public informed and holding the government accountable.
During the past year, EFF’s FOIA team filed over 30 different FOIA requests, to dozens of federal agencies, seeking information on the government's use of technology and its effect on civil liberties. When the government doesn't respond to our requests, we are sometimes forced to file suit: in 2011, we filed three new lawsuits, and are currently litigating four others, stemming from the government's failure to release the records we've requested.
In this post, we’ll highlight some of the documents we’ve received over the past year that shed new light on government activities, ranging from law enforcement guides for getting information from social networking sites, to abuse of federal surveillance laws. Tomorrow, a second post will discuss our three new FOIA lawsuits.
Some of the most important FOIA responses EFF received in 2011 include:
Social Networking Law Enforcement Guidelines
In November, Anonymous made headlines by leaking Facebook’s law enforcement guidelines, which described the company's policy on responding to law enforcement requests. Yet the same guide had been online since January 2011, thanks to EFF's FOIA requests to the Justice Department and a dozen other agencies. EFF received copies of guides from 13 companies, including Facebook, MySpace, AOL, eBay, Ning, Tagged, Craigslist and others, and for some of the companies we received several versions of the guide. These guides gave the public an unprecedented view into how many of the largest social networks respond, and the process they require, for various disclosures to law enforcement.
Along with Berkeley School of Law’s Samuelson Clinic’s, we organized them into a comprehensive spreadsheet (in .xls and .pdf) that compares how the companies handle requests for user information such as contact information, photos, IP logs, friend networks, buying history, and private messages.
You can read EFF’s whole report here, along with Tech Crunch’s explanation of how EFF uncovered this information long before Anonymous did.
Intelligence Oversight Board Members
In 2009, President Obama signed an Executive Order strengthening the Intelligence Oversight Board (IOB)—a Presidentially appointed, independent, civilian oversight board charged with ensuring that intelligence activities comply with applicable laws, executive orders, and internal agency procedures. Yet nearly two years into his administration, President Obama still had not announced any appointments to the IOB – in fact, it was not clear if there were any members on the board at all.
In February 2011, following the White House’s failure to respond to a reporter’s questions concerning the IOB, we submitted a FOIA request to the Director of National Intelligence (DNI) to determine if, in fact, the IOB had members. When EFF didn’t hear anything for 8 months, we sued the DNI for failing to respond to the request. Finally, a week after we filed suit, DNI produced three documents (pdf) that they claimed satisfied our request.
Because of EFF’s lawsuit we now know that David Boren, Chuck Hagel, and Lester Lyles are all currently serving on the IOB. Read more about this important disclosure, and the questions that it raised, here.
Defense Department Intelligence Violations
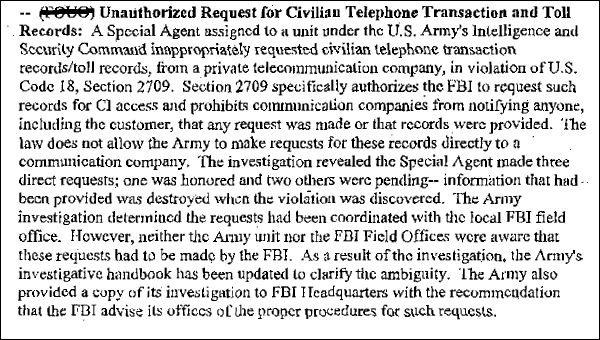
Thanks to the 2011 Supreme Court case Milner v. Department of Navy, which eliminated a legal rationale the government often relied on to keep documents secret, the Defense Department was forced to release more documents from a 2009 Freedom of Information Act (FOIA) lawsuit that we filed against the DoD and a half-dozen other federal agencies involved in intelligence gathering.
The documents revealed Defense Department misconduct, both in concealing the violations in response to the FOIA request and in the violations themselves. One document described attempts by the Army to investigate participants at a conference on Islamic law at the University of Texas Law School.


Other documents showed that the Army issued National Security Letters to telecommunications providers, despite the fact that the Army lacks the legal authority to do so.
Read more about the documents and what else they revealed here.
PATRIOT Act Abuses
Another FOIA request showed FBI Director Robert Mueller may have omitted important information when testifying to Congress about possible abuses of the PATRIOT Act’s investigative authority. In March 2011, during the question and answer portion of Mueller's testimony before the Senate Judiciary Committee, Sen. Chuck Grassley asked the FBI Director: have "any of these [expiring PATRIOT Act] provisions been subject to any negative reports . . . finding abuse?" Mueller responded, "I'm not aware of any."
EFF was. We had submitted a FOIA request for records of violations stemming from the FBI's use of the expiring (though since renewed) provisions of the PATRIOT Act. In the FBI's response to our request, we uncovered evidence of mulitple reports of violations (pdf). However, in typical FBI fashion, the reports are almost entirely redacted. As a result, the details of most of the violations remain secret. However, by cross referencing documents received from another FOIA request to the FBI, we were able to determine, in a case where the FBI’s "John Doe" roving wiretap authority was authorized, the FBI ended up monitoring the conversations of "young children" for "approximately" five days.
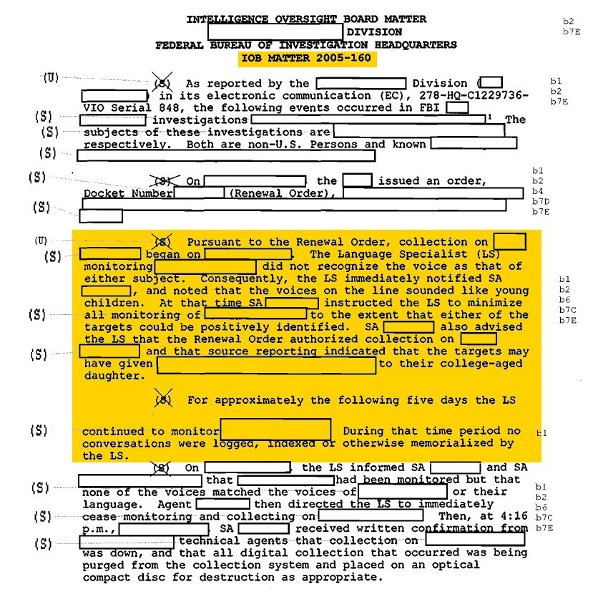
We made these facts available in a letter (pdf) to Sen. Grassley immediately after Director Mueller denied knowing of any such abuses. Read more about this case here.
While the documents EFF received in 2011 helped shine light on government activities, tomorrow, we will detail three of the FOIA lawsuits we filed in 2011 and explain what information we hope the suits will make available -- information about drones, the PATRIOT Act, and FBI surveillance.